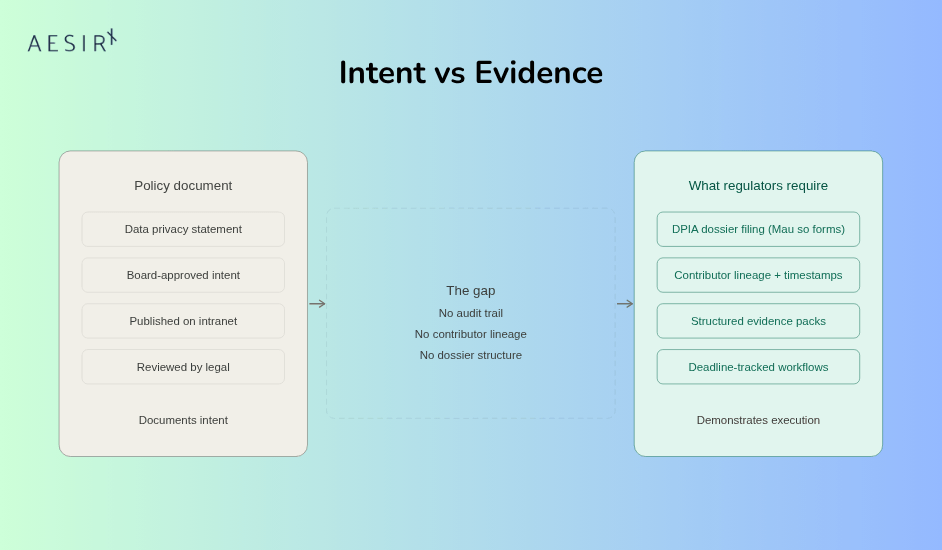
You have a data privacy policy. It was reviewed by legal, approved by the board, and published on the company intranet. When the Ministry of Public Security requests your DPIA dossier filing – complete with Mau so forms, contributor sign-offs, and a submission package validated against statutory requirements – that policy document cannot answer.
This is the gap where organizations operating in Vietnam fail: the distance between "we have a policy" and "we can respond to a regulator."
The Problem: Six Frameworks, Zero Operational Readiness
Vietnam does not have a single data protection law. It has six overlapping regulatory frameworks administered by different government authorities, each imposing distinct obligations:
- Law 91/2025/QH15 - Vietnam Personal Data Protection Law (PDPL) – personal data protection, administered by the Ministry of Public Security.
- E-Commerce Law 2025 – consumer data obligations under the Ministry of Industry and Trade.
- Telecommunications Law 2023 – subscriber data requirements under the Ministry of Information and Communications.
- Data Law 60/2024/QH15 – national data governance framework.
- Cybersecurity Law 2025 – security incident obligations.
- AI Law 2026 - emerging AI governance requirements.
Each framework carries its own filing requirements, dossier formats, authority interaction protocols, and response deadlines. A policy document addresses none of these operational demands.
What Regulators Actually Require
Consider the PDPL (Law 91/2025/QH15) alone. Compliance is not a statement of intent. It requires:
- DPIA dossier filing to the Ministry of Public Security, assembled from inputs across legal, IT security, HR, marketing, and procurement.
- Data subject rights fulfillment - receiving, processing, and responding to access, correction, and deletion requests within defined windows.
- Cross-border transfer impact assessments routed through defined authority channels.
- Breach notification within statutory timelines.
In addition, under PDPL, Decree 356/2025/NĐ-CP specifies the mechanics through the official Mẫu số set, including Mẫu số 01a/01b for cross-border transfer dossier submission, Mẫu số 02a/02b for personal data processing impact dossier submission, Mẫu số 03a/03b for dossier updates, Mẫu số 08 for breach notification, and Mẫu số 09/10 for the impact assessment reports themselves. These are not optional formatting suggestions. They define the filing instruments and dossier structures regulators expect when reviewing submissions.
The deadlines are concrete and procedural. Once authorities request additional information, completion, or correction, the organization can quickly lose its practical filing window if evidence and ownership are scattered.
Where the Gap Appears
A policy document does not generate audit trails. It does not track which department contributed which section of a DPIA dossier, or whether that contribution was reviewed before submission. It does not produce evidence packs that demonstrate operational compliance across six frameworks simultaneously.
In practice, the operational pain is specific: different business units submit inconsistent inputs, filing status has no single source of truth, accountability gaps appear when contributions are late or incomplete, and dossier packages are assembled manually when they should be structured and version-controlled.
The audit problem is just as concrete: evidence has to be pulled from multiple stakeholders, evaluations have to be measured consistently across frameworks, and gap findings need traceable documentation linking each observation to a specific regulatory requirement.
Why This Matters Now
Three developments have compressed the timeline for organizations to move from policy to operations.
Enforcement infrastructure is active. The Ministry of Public Security has established the operational apparatus for PDPL enforcement. The filing procedures defined in Decree 356 are not theoretical – they are the administrative reality that organizations face when interacting with regulators.
Framework overlap creates compounding obligations. An organization processing personal data in e-commerce is not subject to one framework. It faces obligations under the PDPL, the E-Commerce Law, potentially the Telecommunications Law, the Data Law, and the Cybersecurity Law simultaneously. Each requires its own evidence of compliance. Policy documents do not scale across this matrix.
Cross-border operations raise the stakes. Vietnam's PDPL requires impact assessments for cross-border data transfers. For multinational organizations or Vietnamese companies with international operations, this means producing transfer impact documentation that satisfies MPS requirements – documentation that must be assembled from operational data, not policy statements.
The organizations most exposed are those that invested in policy creation but stopped short of building the operational infrastructure to execute against those policies. They have the right words on paper and no mechanism to turn those words into filed dossiers, tracked evidence, or auditable workflows.
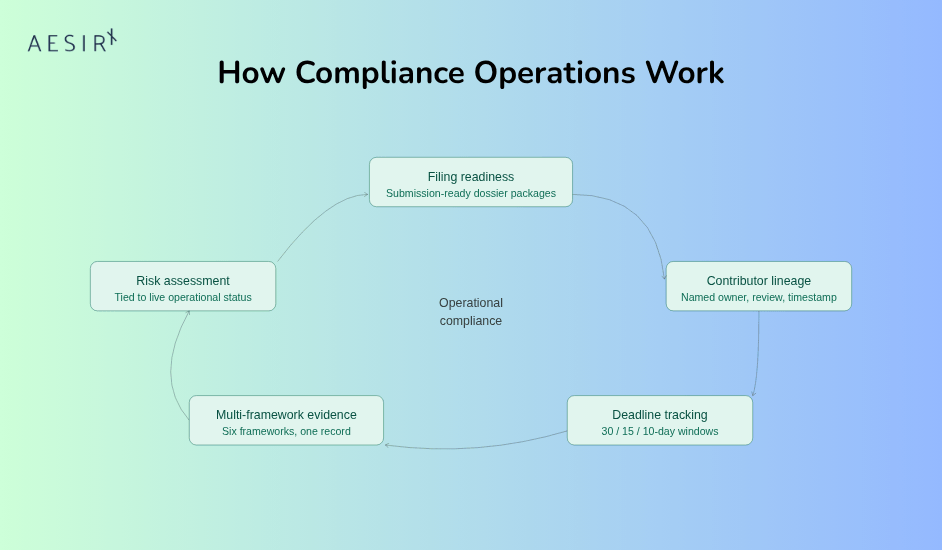
What Structured Compliance Operations Look Like
The shift from policy-based to operations-based compliance is not abstract. It involves specific capabilities that policy documents cannot provide.
Filing readiness, not filing intent.
An operational compliance system produces submission-ready dossier packages using the correct official Mẫu số forms and supporting dossier components. When MPS requests a DPIA filing, the organization produces a structured package – not a scramble across email threads and shared drives.
Contributor lineage and accountability.
Every section of a compliance dossier should trace to a named contributor, a review step, and a timestamp. When a regulator asks who prepared the data mapping section of a DPIA and when it was last reviewed, the answer should be immediate and verifiable.
Multi-framework evidence management.
A single business process - say, customer data collection in an e-commerce operation - may generate compliance obligations under four or five frameworks. Operational compliance means producing framework-specific evidence from shared operational data, without duplicating effort or losing traceability.
Deadline tracking with statutory precision.
The 30-day, 15-day, and 10-day windows defined in Decree 356 are not guidelines. They are procedural deadlines that, if missed, require restarting the filing process. Operational compliance tracks these windows, assigns responsibility for each stage, and escalates when deadlines approach.
Risk assessment integrated with operations.
Compliance risk is not a static score assigned during an annual review. It is a dynamic measure that changes as filing deadlines approach, as regulatory requirements shift across frameworks, and as organizational processes evolve. Risk assessment connected to operational data reflects actual exposure, not estimated exposure.
How ComplianceOne Supports This
AesirX ComplianceOne is a 27-module platform (3 core + 24 configurable) built for operational compliance. For organizations navigating Vietnam's regulatory environment, the relevant capabilities include:
-
Compliance forms module
Pre-configured templates aligned to Decree 356's official Mẫu số forms and the supporting dossier components those filings require. Templates are structured to match regulatory expectations, reducing the risk of submission rejection due to formatting or completeness errors.
-
DPIA assessment workflows
Structured dossier assembly across departments, with named owners, review checkpoints, and deadline tracking built into the workflow. Each contribution is recorded with identity and timestamp, creating the traceable lineage regulators and auditors expect.
-
Audit trail with contributor lineage
Every action (a field edit, a review approval, a submission) is recorded with who, what, and when. This is the operational evidence layer that transforms a policy commitment into a demonstrable compliance practice.
-
Task and workflow management
Filing workflows are broken into clear tasks with deadlines, dependencies, and escalation paths. When a department misses a contribution deadline, the gap is surfaced before it turns into a missed filing window.
-
Multi-framework coordination
One operational view across Vietnam’s overlapping regulatory frameworks. When a single business process triggers obligations under multiple regimes, the platform tracks each requirement separately while reusing the same underlying operational evidence.
-
Risk assessment tied to operational status
Compliance risk scores derived from actual filing status, deadline proximity, evidence completeness, and framework coverage – not from annual questionnaire responses.
Key Takeaways
- Policy is necessary but not sufficient. Vietnam's regulatory model requires operational proof, filed dossiers, structured evidence, tracked workflows, not just documented intent.
- Six frameworks mean six evidence streams. Each Vietnamese regulatory framework requires its own compliance evidence. Manual processes do not scale across this matrix without gaps.
- Deadlines are procedural, not advisory. The statutory windows in Decree 356 (30-day reviews, 15-day supplements, 10-day resubmissions) reset the filing cycle if missed. Deadline management must be systematic.
- Contributor lineage is an audit requirement. Regulators and internal auditors need to see who contributed what, when, and whether it was reviewed. Policy documents do not provide this traceability.
- Operational compliance reduces the cost of regulatory interaction. When a regulator or auditor asks a question, the answer should come from the system, not from a cross-departmental scramble.
Next Steps
Start a 30-day pilot. Deploy ComplianceOne against one framework – the PDPL is the natural starting point – and measure the gap between your current operational readiness and what the platform produces. The pilot includes framework configuration, form setup, and a filing readiness assessment.
Request a pilot
Schedule a compliance operations consultation. Walk through your current policy-to-operations gap with a compliance specialist. The consultation covers your framework obligations, current filing readiness, and a structured path from policy documentation to operational compliance.




