An enterprise DPO managing compliance across six Vietnamese regulatory frameworks does not need another dashboard. They need a way to decompose regulatory obligations into departmental tasks, track contributor inputs across business units, and produce filing-ready dossiers without a two-week assembly scramble every quarter. The gap between knowing what compliance requires and having the operational infrastructure to execute it is where most enterprise teams stall.
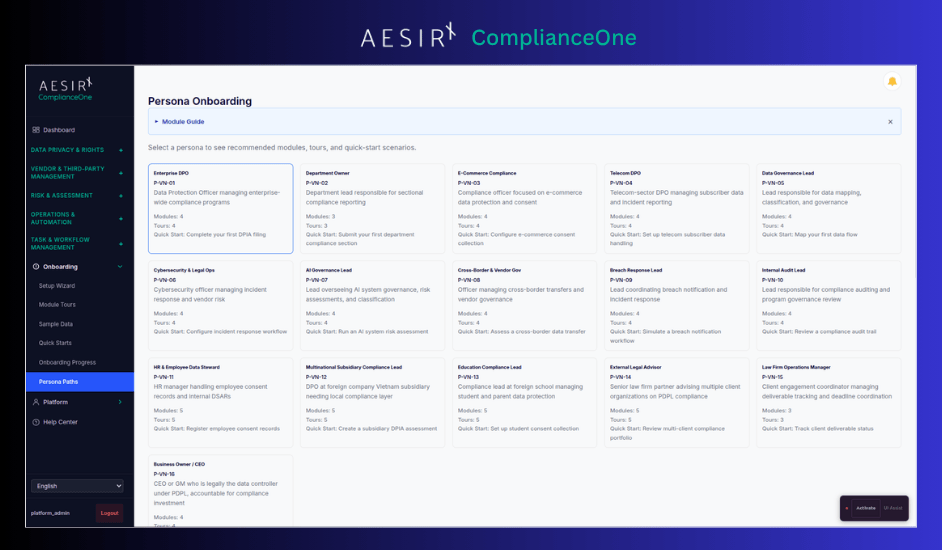
This post walks through how ComplianceOne's module structure maps to that operational reality, not as a feature tour, but as an explanation of how 28 modules across 5 categories address the specific challenges that enterprise compliance teams face in Vietnam.
The Problem: Compliance Teams Without Compliance Infrastructure
Enterprise compliance teams in Vietnam operate under a specific set of pressures that general-purpose tools were not designed to address.
Scattered inputs, no single source of truth. A DPIA dossier filing requires coordinated inputs from legal, IT security, HR, marketing, and procurement. In most organizations, these inputs arrive via email, shared drives, and spreadsheets maintained by individual departments. The DPO's job becomes chasing department heads for contributions that should have been captured in a structured workflow weeks earlier.
Cybersecurity and legal operations overlap. When a data breach triggers both incident response obligations under the Cybersecurity Law and notification requirements under the PDPL, the CISO and legal counsel need coordinated workflows, not parallel processes in disconnected tools. The cybersecurity team tracks technical containment. The legal team tracks regulatory notification. Neither team has visibility into the other's progress, and the filing deadline does not wait for them to reconcile.
Manual dossier assembly under deadline pressure. Regulatory filing windows are procedural: 30-day reviews, 15-day supplement periods, 10-day resubmission windows. Organizations that assemble dossiers manually routinely miss these windows, not because the substance is missing, but because the assembly process has no structural support.
No contributor lineage across departments. Auditors and regulators increasingly expect to see not just the completed filing, but the chain of who contributed each section, who reviewed it, who approved it, and when each step occurred. A signed PDF does not provide this. Reconstructing it from email timestamps and file metadata is unreliable and time-consuming.
Why This Matters Now
Vietnam's regulatory environment is not converging toward simplicity. Six frameworks administered by different government authorities impose distinct obligations, filing formats, and interaction protocols. The PDPL alone requires DPIA dossier filings with 13 administrative procedure forms and 8 statutory annexes. The Cybersecurity Law imposes separate incident reporting obligations. The E-Commerce Law adds consumer data requirements under a different ministry.
For enterprise teams operating across multiple regulatory frameworks, the question is no longer whether to invest in compliance infrastructure. It is whether the infrastructure they choose can handle the operational complexity – multi-framework obligations, multi-department coordination, structured filing production – without requiring the compliance team to become systems integrators stitching together tools that were never designed to work together.
How ComplianceOne Maps to Compliance Operations
ComplianceOne is a 28-module platform: 4 core infrastructure modules and 24 configurable modules organized into 5 buyer-facing categories. Each category maps to a distinct operational domain. The structure is not arbitrary, it reflects how enterprise compliance teams actually divide their work.
1. Data Privacy & Rights
Seven modules handle the operational side of data subject interactions and data governance.
Data Mapping captures where personal data resides across the organization.
Classification and Data Discovery provide the inventory layer that feeds into DPIA assessments and cross-border transfer evaluations.
Consent tracks consent status across processing activities. Consent Properties defines the attributes and configuration that underpin each consent record.
Data Subjects creates a unified profile per individual that aggregates all rights request cases, consent workflows, and privacy interactions into a single chronological timeline. When a regulator asks for a complete record of everything the organization holds on a specific person, the answer is a single profile lookup rather than a manual cross-module assembly.
Rights Requests manages the intake, routing, and fulfillment of data subject access, correction, and deletion requests. Each request carries a timeline, assigned handlers, and an evidence trail showing how the organization responded. This is the difference between "we handle requests" and "we can demonstrate systematic handling with response time records."
For the enterprise DPO, this category answers a specific question: when a regulator asks about your data processing inventory and consent basis, can you produce the answer from a structured record, or do you need to survey department heads?
2. Vendor & Third-Party Management
Two modules address the governance and risk dimensions of third-party relationships.
Vendor Governance structures the lifecycle of vendor relationships from onboarding through ongoing oversight – contract terms, data processing agreements, compliance status tracking, and renewal management. Vendor Risk handles the assessment side: risk scoring, due diligence records, and periodic reassessment workflows.
For procurement teams responsible for vendor onboarding, these modules provide the compliance layer that procurement workflows typically lack. When a vendor processes personal data on behalf of the organization, the PDPL imposes specific obligations on the data controller. Vendor Governance captures whether those obligations are contractually addressed and operationally monitored, not just at onboarding, but throughout the relationship.
3. Risk & Assessment
Four modules cover the assessment, monitoring, and accountability functions that underpin regulatory filings.
Privacy Scanner provides automated detection capabilities.
DPIA & Assessments handles the structured assessment workflows required under the PDPL – impact assessments that draw inputs from across the organization, route through defined review chains, and produce filing-ready output.
Incidents manages the intake and structured record of data breach and security incidents, capturing what occurred, when it was identified, and the evidence trail that feeds into both regulatory notification and internal response workflows.
Audit Trail captures every action across the platform with a 4-role contributor chain: contributor, reviewer, approver, and submitter.
Taken together, this risk and assessment category addresses the operational cycle that most compliance teams find hardest to sustain: not the initial assessment, but the ongoing monitoring, reassessment, and evidence accumulation that regulators expect between filing periods.
4. Operations & Automation
Seven modules handle the operational workflows that compliance teams manage daily.
Connectors provide integration points with external systems.
Localization supports the 16-locale infrastructure required for organizations operating across Vietnamese and international markets.
Compliance Forms provide structured templates aligned to regulatory requirements, including the specific forms and annexes required under Decree 356.
Deletion Orchestration manages the operational complexity of data deletion requests that span multiple systems and data stores.
Incident Operations handles the internal coordination when a data breach or security incident occurs: containment actions, technical investigation, and stakeholder communication. It works in tandem with the Incidents module in Risk & Assessment, which manages the regulatory notification workflow – timelines, authority communications, and evidence assembly. For the CISO managing a breach that triggers both Cybersecurity Law and PDPL obligations, these modules provide coordinated workflows across both categories rather than parallel processes in disconnected tools.
Monitoring Programs and Program Governance provide the ongoing oversight layer: scheduled reviews, KPI tracking against compliance baselines, and governance structures that define who is accountable for what.
5. Task & Workflow Management
Four modules provide the structural layer that every other category depends on.
Organizations handles the multi-entity dimension: corporate group governance, organizational hierarchy, and shared reference data across subsidiaries. For enterprises operating multiple legal entities under a common compliance framework, this task and workflow layer provides the structural backbone that prevents each entity from operating in isolation.
Task Management decomposes compliance obligations into assigned tasks with deadlines, dependencies, and escalation rules.
Access Accountability addresses the intersection of access management and compliance – documenting who has access to what data, under what authority, and whether that access remains appropriate. For organizations operating under the Cybersecurity Law's access logging requirements, this module provides the structured record that periodic audits require.
Partner Workspace extends operational workflows to external partners who contribute to compliance processes.
Cross-Cutting Capabilities
Beyond the category structure, four capabilities span the entire platform.
Audit Trail with Contributor Lineage
Every module writes to a shared audit trail that records the 4-role contributor chain: who contributed a specific record, who reviewed it, who approved it, and who submitted it to the relevant authority. This is not a log file. It is the evidentiary infrastructure that transforms compliance activity into auditable evidence. When a regulator asks who prepared the risk assessment section of a DPIA dossier, the answer is a structured lookup, not a reconstruction from email threads.
Role-Based Access Control (392 Permissions, 7 Roles)
The RBAC model maps to compliance organizational reality. A department contributor can submit inputs for their section of a filing. A compliance officer can review those inputs. A DPO can approve them. A designated submitter can file them with regulatory authorities. These are not abstract permission levels – they reflect the actual accountability chain that regulators expect to see in filing records.
Multi-Framework Support
ComplianceOne supports 6 Vietnamese regulatory frameworks and 30 EU/EEA market packs. Framework-to-module linkage means that when a regulatory obligation maps to a specific compliance activity, the platform connects the framework requirement to the operational module that addresses it. This is particularly relevant for organizations subject to multiple overlapping frameworks – the PDPL, the Cybersecurity Law, and the E-Commerce Law may all impose obligations triggered by a single business process.
Filing Readiness
Dossier assembly, submission packages, and evidence packs are produced from existing structured records, not assembled under deadline pressure from scattered sources. The filing readiness layer draws from audit trail records, form submissions, assessment outputs, and contributor lineage to produce submission-ready packages aligned to the specific format each regulatory authority requires.
Key Takeaways
- Module structure maps to operational domains, not feature categories. The 5 buyer-facing categories reflect how compliance teams actually divide their work: privacy operations, vendor oversight, risk assessment, daily operations, and workflow management. Each category addresses a distinct set of regulatory obligations.
- Cross-department coordination requires structural support. When a DPIA dossier needs inputs from five departments, the infrastructure must track who has contributed, who has not, and what is overdue, before the filing deadline arrives, not after.
- Incident response coordination is a multi-team problem. Cybersecurity and legal operations must work from coordinated workflows when a breach triggers obligations under multiple frameworks simultaneously. Parallel processes in disconnected tools produce compliance gaps.
- Filing readiness should be the default state, not a sprint. Dossier assembly from structured records with complete contributor lineage is a fundamentally different operation from manual assembly under deadline pressure. The difference is infrastructure, not effort.
- Contributor lineage is non-negotiable for audit defense. Regulators and auditors expect to see the complete chain – who contributed, who reviewed, who approved, when each step occurred. A platform that captures this as a byproduct of work eliminates the most time-consuming part of audit preparation.
Frequently Asked Questions About Compliance Infrastructure for Enterprise Teams
Next Steps
Start a 30-day pilot.
Deploy ComplianceOne against a specific compliance workflow, a multi-department DPIA dossier, a vendor governance lifecycle, or a cross-framework incident response scenario. Measure the difference between your current process and a structured operational model. The pilot includes module configuration, workflow setup, and a compliance operations baseline assessment.
Schedule a compliance operations consultation.
Walk through your current operational state with a compliance specialist. The consultation maps your existing compliance workflows across the 5 operational domains, identifies structural gaps, and defines a prioritized implementation path based on your regulatory obligations and filing timelines.




