DPO Radio
AesirX ComplianceOne | Vietnam Cybersecurity Law
Why the Vietnam Cybersecurity Law Matters
The Vietnam Cybersecurity Law 2025 (Law 116/2025/QH15) is the consolidated cybersecurity framework replacing the earlier Law 24/2018. Administered by the Ministry of Public Security (MPS), it becomes effective on 2026-07-01 and expands the scope of cybersecurity obligations for organizations operating in Vietnam. The law covers incident escalation and response, authority cooperation, data localization requirements, in-scope determination, and operational security measures.
For organizations subject to this law, the operational obligations are substantial. Cybersecurity incidents must be detected, assessed, escalated, and reported to authorities through defined channels with evidence preserved at every step. Authority cooperation extends beyond incident response – organizations may receive requests for information, system access, or operational data, each requiring verification, legal review, and documented handling. The law expands the earlier cybersecurity framework's scope to cover more organization types and service categories.
Data localization remains a core obligation. Organizations that fall within the law's scope must assess their data localization requirements, document their compliance status, and maintain evidence of compliant data storage and retention practices. The in-scope determination process (previously defined under Decree 53/2022/ND-CP) requires organizations to evaluate their status based on service type, user count, and data types, and to document that evaluation with supporting evidence.
The cybersecurity law's obligations overlap significantly with other Vietnam frameworks. An organization processing personal data is subject to both the Cybersecurity Law and the PDPL. A telecom operator faces the Cybersecurity Law alongside the Telecom Law. Managing these overlapping incident response, authority cooperation, and data governance obligations across disconnected tools creates gaps in evidence chains, inconsistent reporting, and accountability breakdowns during high-pressure incident situations where structured operations matter most.
What the Vietnam Cybersecurity Law Covers
Dimension
Coverage
Scope
Organizations operating information systems, online services, or digital infrastructure in Vietnam, with expanded scope from the predecessor law
Affected organizations
Domestic enterprises, foreign entities operating in Vietnam, critical information infrastructure operators, online service providers, digital platform operators
Key obligations
Cybersecurity incident detection and escalation, authority notification and cooperation, data localization assessment and compliance, in-scope determination documentation, operational security measures, vendor security assessment, periodic security review
Evidence requirements
Incident case records with evidence chain of custody, authority interaction logs, data localization compliance documentation, in-scope determination records, security measure implementation evidence, vendor security assessment records, audit trails for all cybersecurity operations
Filing/submission
Incident notifications and authority responses through MPS-defined channels, data localization compliance documentation
Deadlines
Incident notification timelines per severity classification, authority request response within policy-defined SLA, ongoing compliance with security measures and data localization
Decrees and Procedures
The cybersecurity compliance landscape spans current requirements and upcoming enforcement changes. Understanding the full picture matters.
Vietnam Cybersecurity Law 2025 (116/2025/QH15)
Vietnam Cybersecurity Law (24/2018 era)
activeDecree 53 – Cybersecurity Law Implementation
activeDraft Enforcement Decree 2026
draft
How ComplianceOne Supports the Vietnam Cybersecurity Law
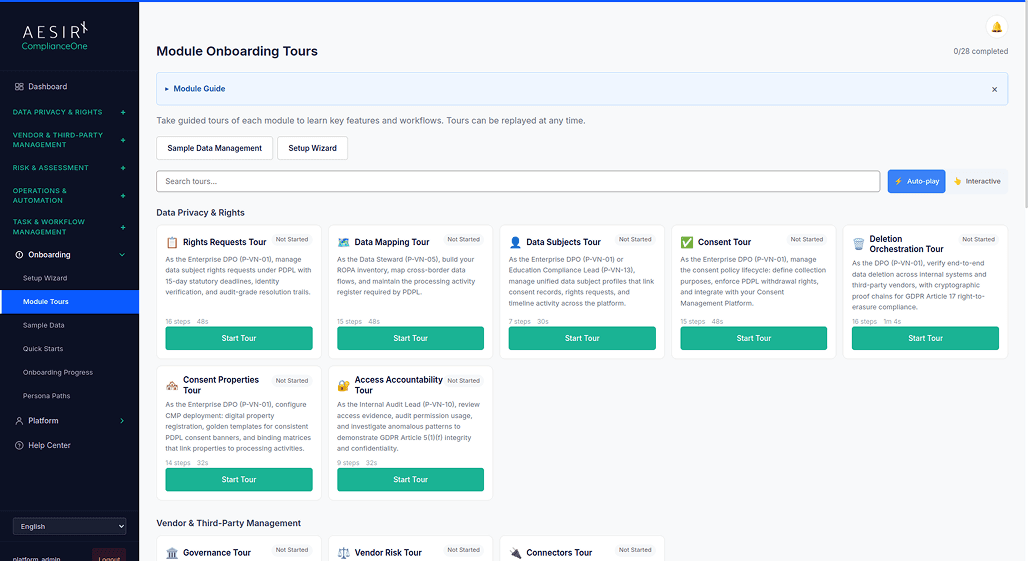
ComplianceOne provides structured incident operations and authority cooperation workflows for cybersecurity compliance. The Incident Operations module manages case-based workflows for cybersecurity incidents: detection, triage, escalation, authority notification, investigation, remediation, and closure. Each case maintains an evidence chain of custody, ensuring that every piece of evidence collected during an incident is tracked with timestamps, contributor identity, and integrity hashes. The Incident Response module handles the notification and authority interaction components, managing communication with MPS and other authorities through defined channels.
Authority cooperation extends beyond incident response. The Monitoring Programs module manages authority requests for information, system access, or operational data. Each request follows a structured workflow – receipt, verification, legal review, management approval, response execution, and closure – with disclosure logging that captures the recipient, scope, legal basis, and approval chain. This centralized authority interaction record satisfies the law's requirement for documented, accountable cooperation.
The Access Accountability module supports the operational security measures required by the law, including access control documentation, role-based permissions evidence, and activity monitoring. Data localization readiness is managed through governance workflows that document in-scope determination, localization assessment, and ongoing compliance status. Vendor security assessment (UC-VN-14) ensures third-party risk is evaluated and documented as part of the organization's cybersecurity posture.
For organizations subject to multiple Vietnam frameworks, all cybersecurity operations are managed within ComplianceOne's shared workflow engine alongside PDPL, Telecom Law, and other framework obligations. Cross-framework inspection readiness (UC-VN-09) ensures comprehensive evidence packs can be produced covering all applicable frameworks. The platform includes 35 internal operational templates for cybersecurity compliance documentation.
Related Modules
Incident Operations
Manages cybersecurity incident case workflows with evidence chain of custody and escalation tracking.
Explore Incident OperationsIncident Response
Handles authority notification, communication management, and incident resolution workflows.
Explore Data ClassificationMonitoring Programs
Manages authority request lifecycle with verification gates, approval workflows, and disclosure logging.
Explore Monitoring ProgramsAccess Accountability
Documents access controls, role-based permissions, and activity monitoring for security compliance.
Explore Access AccountabilityAudit Trail
Captures tamper-evident records of incident handling, authority interactions, and security operations.
Explore Audit TrailProgram Governance
Manages security policies, in-scope determination, data localization documentation, and review schedules.
Explore Program GovernanceCompare the Difference

Without Structured Framework Operations

With ComplianceOne
Built for Cybersecurity Law Compliance Operations
ComplianceOne supports cybersecurity incident operations with case-based workflows that maintain evidence chain of custody from detection through remediation and closure, addressing the law's requirement for documented, accountable incident handling.
The platform includes 35 internal operational templates for cybersecurity compliance documentation, covering incident records, authority cooperation logs, data localization assessments, security measure evidence, and vendor security evaluations.
Seven Vietnam regulatory frameworks are managed within a shared workflow engine, enabling organizations subject to overlapping cybersecurity, data protection, and sector-specific obligations to maintain consistent evidence production and audit trail coverage across all frameworks.
See Vietnam Cybersecurity Law Compliance in Action
Ready to see how ComplianceOne manages cybersecurity obligations operationally? Request a demo tailored to your organization's needs.
People Also Ask
The Vietnam Cybersecurity Law 2025 (Law 116/2025/QH15) becomes effective on 2026-07-01. It replaces the earlier Law 24/2018 with expanded scope and updated obligations. Organizations should begin preparatory compliance assessments ahead of the effective date.
The Incident Operations module manages the full incident lifecycle: detection, triage, escalation based on severity classification, authority notification through defined channels, investigation with evidence collection, remediation tracking, and case closure. Evidence chain of custody is maintained throughout, with tamper-evident records of every action.
Yes. The Monitoring Programs module manages all types of authority requests — information requests, system access requests, operational data requests — through a structured workflow with verification, legal review, management approval, response execution, and closure. Every interaction is logged in a centralized disclosure register.
Data localization readiness is managed through the Program Governance module with governance workflows that document in-scope determination (based on service type, user count, and data types), localization assessment, compliance status, and ongoing review schedules. Evidence of compliant storage and retention practices is maintained with audit trail coverage.
Yes. ComplianceOne supports 7 Vietnam regulatory frameworks within a shared workflow engine. Organizations subject to both the Cybersecurity Law and the PDPL manage all obligations from a single platform. When a cybersecurity incident also involves a personal data breach, both the cybersecurity incident workflow and the PDPL breach notification workflow operate in coordination with consistent evidence production.
Next Steps

Start a Compliance Pilot
Test cybersecurity compliance workflows with your team – incident operations, authority cooperation, and evidence generation.

Discuss Your Compliance Needs
Talk to our team about cybersecurity compliance operations, multi-framework coverage, and deployment for your organization.








