DPO Radio
AesirX Incident Operations
Why Incident Operations Matters
Incident response at scale requires more than a case-tracking system. Organizations managing cybersecurity incidents under Vietnam's Cybersecurity Law and data breaches under the PDPL face overlapping regulatory timelines, multi-team coordination demands, and strict evidence requirements. Without standardized operational procedures, each incident is handled differently, leading to inconsistent severity assessments, missed SLA windows, and evidence gaps that surface during regulatory review.
Cybersecurity and Legal Operations Leads (P-VN-06) need scenario-based playbooks that define exactly what happens at each stage of an incident – who is notified, what evidence is collected, and which escalation paths apply. Breach Response Leads (P-VN-09) need playbooks that connect directly to breach notification workflows so that confirmed breaches automatically trigger the regulatory filing process without manual handoffs.
When organizations rely on ad hoc response procedures, the consequences are predictable: response teams waste time deciding what to do instead of executing, SLA clocks expire because no one is tracking them centrally, evidence is collected inconsistently and cannot be assembled into a coherent package for regulators, and post-incident reviews either do not happen or produce no actionable improvements.
AesirX ComplianceOne Incident Operations provides playbook-based response standardization, configurable SLA definitions with pre-loaded PDPL defaults, a coordination dashboard for multi-team visibility, playbook-to-notification linkage that automates breach notification triggers, evidence chain of custody with tamper-evident records, and post-incident review with formal sign-off. The module serves both cybersecurity incident workflows (UC-VN-05) and breach notification operations (UC-VN-08), giving security and compliance teams a shared operational foundation.
How It Works
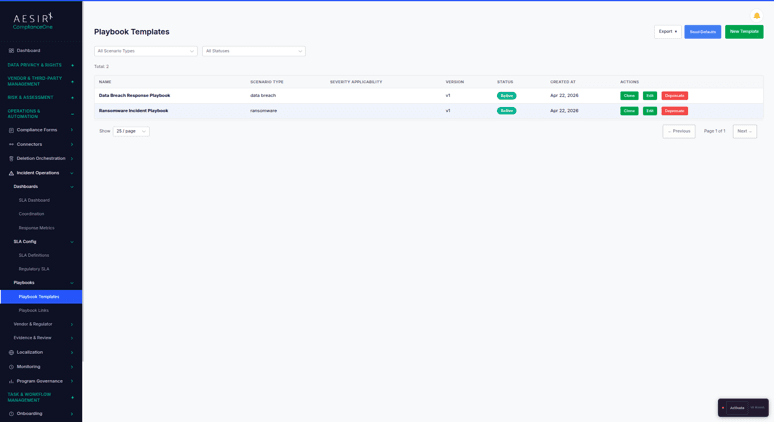
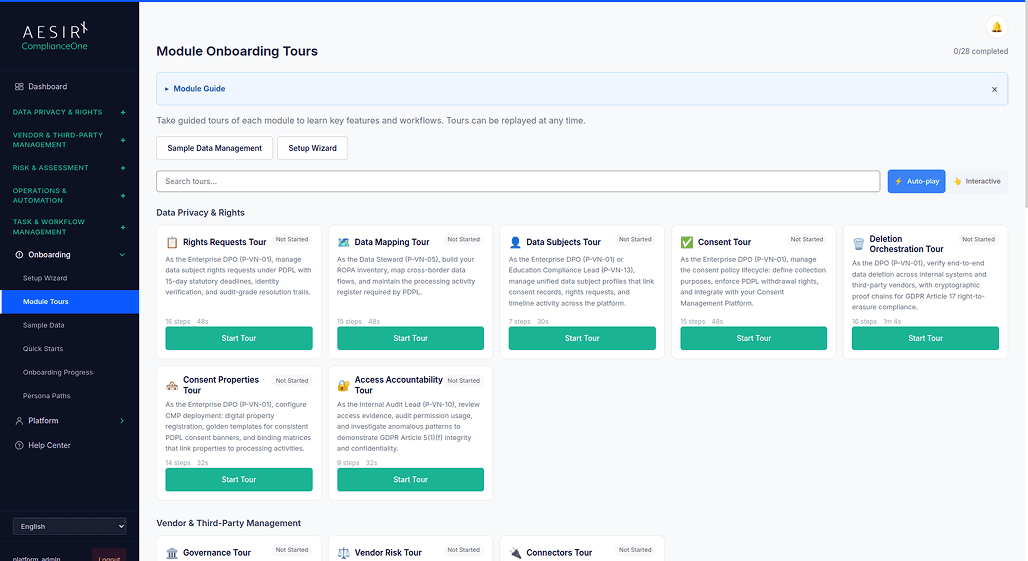
Incident Playbooks
Scenario-based response playbooks define the step-by-step procedures for different incident types – ransomware, unauthorized access, data exfiltration, insider threat, and more. Each playbook specifies required actions, responsible roles, evidence collection points, and escalation triggers. Teams execute against a defined plan rather than improvising under pressure.
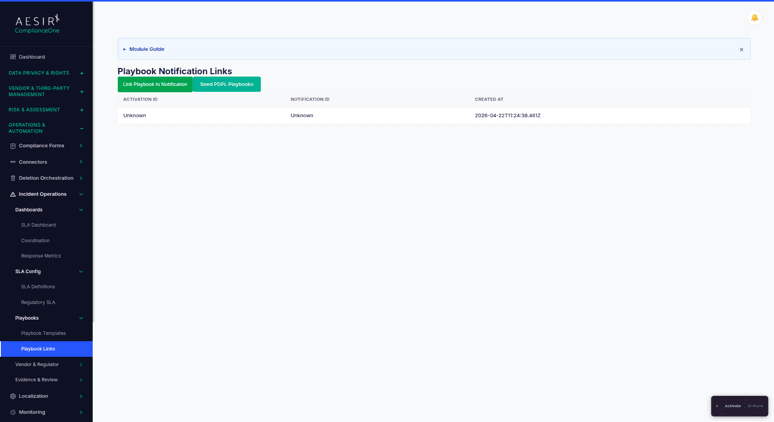
Playbook-to-Notification Linkage
Playbook steps can automatically trigger breach notification workflows when a breach determination is confirmed. This eliminates the manual handoff between incident response and regulatory notification – when the playbook reaches the "breach confirmed" stage, the notification lifecycle in Incident Response is initiated automatically.
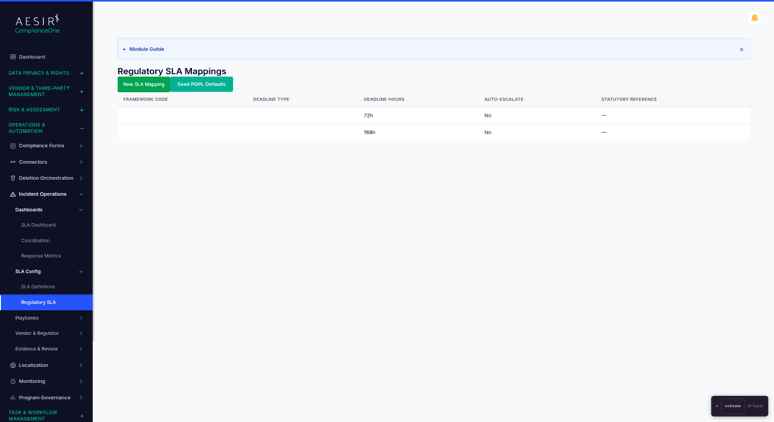
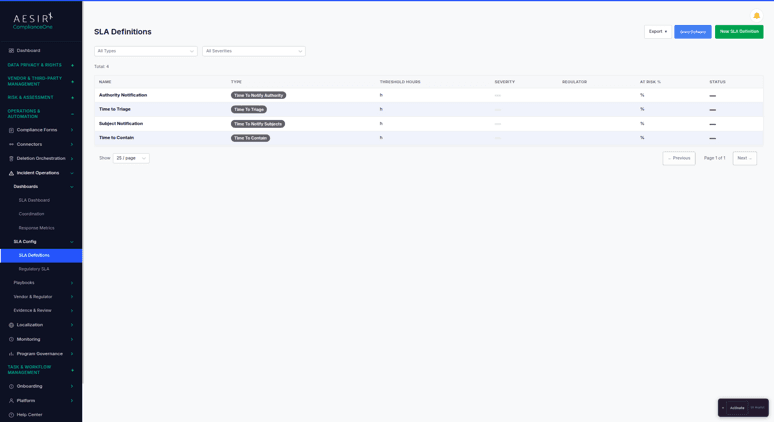
Regulatory SLA Mapping
Pre-configured PDPL SLA defaults (72-hour initial notification and 360-hour supplement) are built in, with configurable overrides for other frameworks. SLA definitions apply automatically to incidents based on their classification and applicable regulatory framework, ensuring deadline tracking starts the moment an incident is classified.
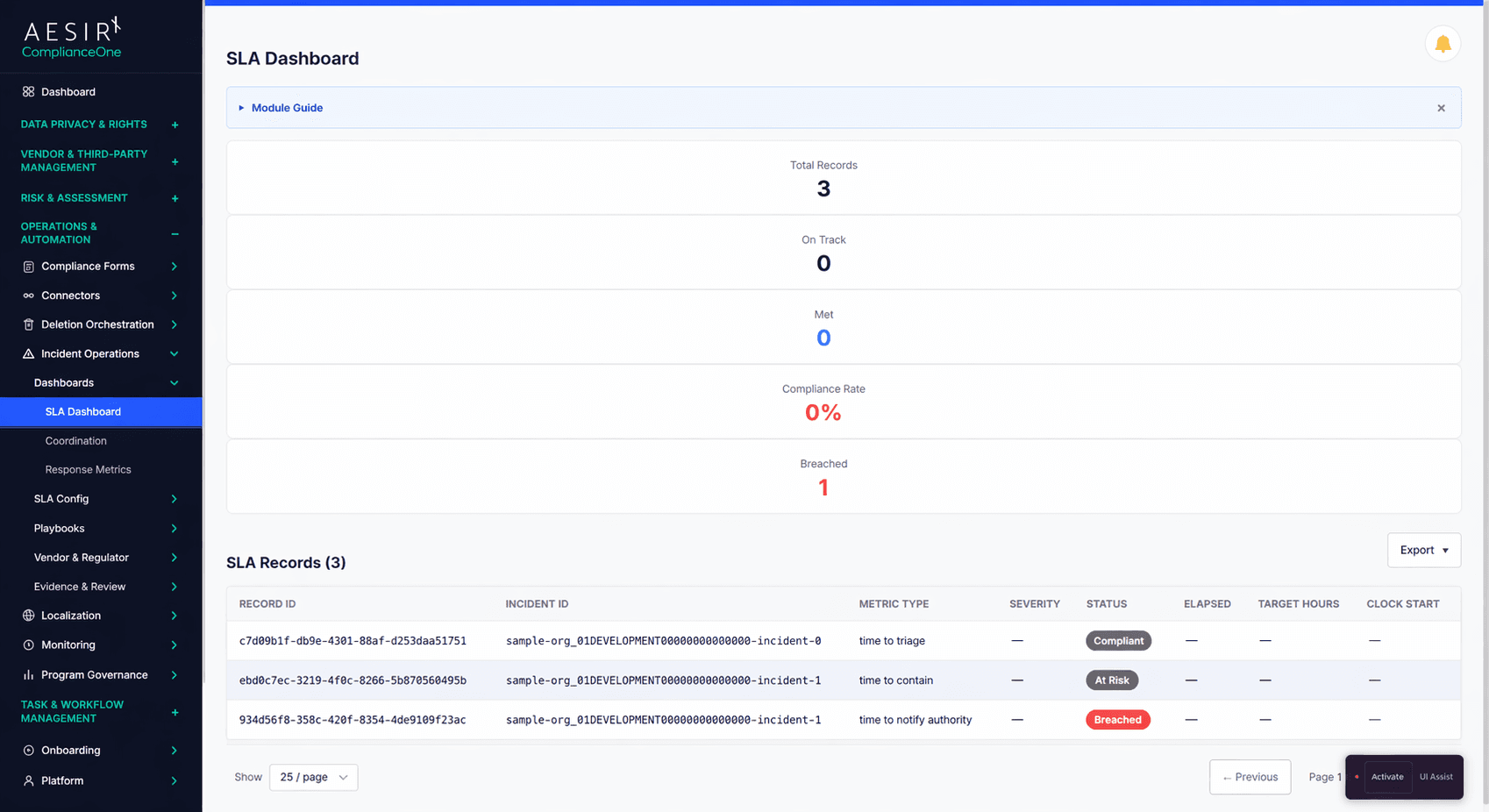
SLA Dashboard
Real-time SLA tracking and visualization shows every active incident's deadline status – on track, at risk, or breached. The dashboard provides both individual incident detail and portfolio-level views so operations leads can prioritize where attention is needed.
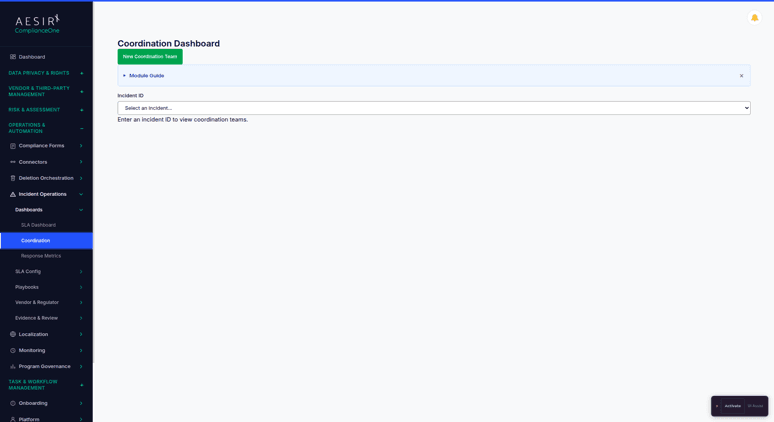
Coordination Dashboard
A unified view of team assignments, SLA clocks, and escalation status across all active incidents. The coordination dashboard gives operations leads visibility into who is working on what, which SLAs are closest to expiry, and which incidents have triggered escalation.
Escalation Workflows
Automated escalation rules trigger notifications when incidents meet defined criteria – SLA approaching expiry, severity escalation, or lack of activity within a defined period. Escalation paths route to the appropriate authority level based on incident classification and organizational hierarchy.
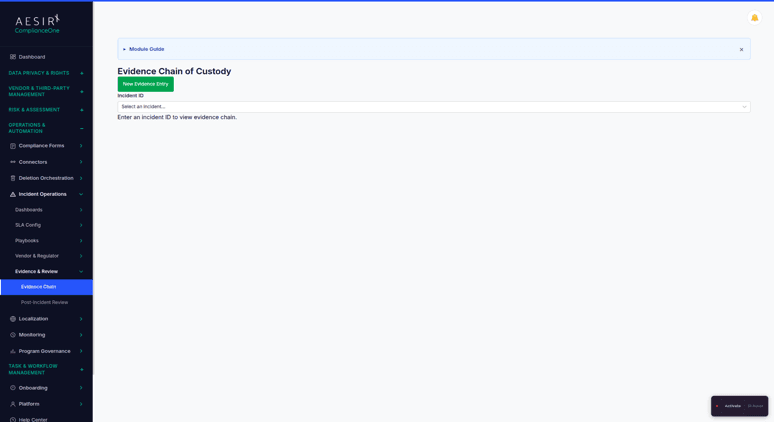
Evidence Chain of Custody
A tamper-evident evidence record is maintained throughout the incident lifecycle. Every piece of evidence – logs, screenshots, communications, forensic artifacts – is tracked with collection timestamp, collector identity, and custody transfers. The chain culminates in a post-incident review with formal sign-off.
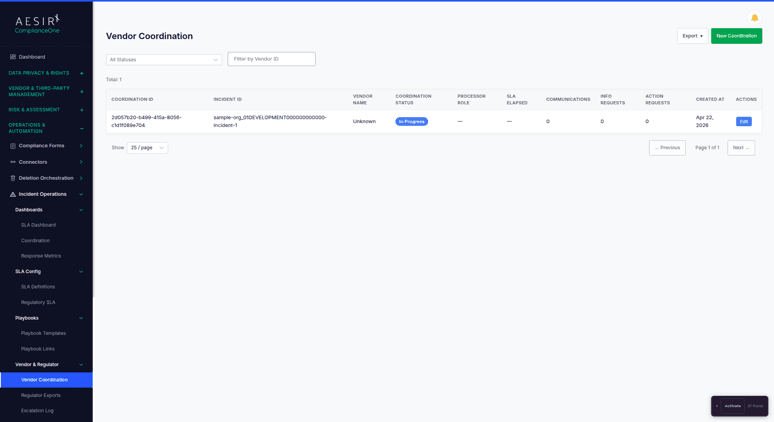
Vendor Coordination
Coordinate incident response activities with vendors when third-party systems are involved. Track vendor acknowledgment, response actions, and evidence submissions within the same incident workflow.
Compare the Difference

Without Incident Operations

With Incident Operations
Built for Real Compliance Operations
Pre-configured PDPL SLA defaults (72-hour initial notification, 360-hour supplement) are built into the SLA engine, reducing setup time and ensuring regulatory deadlines are tracked from day one.
Playbook-to-notification linkage eliminates the manual handoff between incident response and regulatory filing, the single largest source of notification delays in manual processes.
Evidence chain of custody with tamper-evident records provides a verifiable evidence trail that meets the standard regulators expect during inspections and authority cooperation requests.
Regulatory Framework Support
Framework
How Incident Operations Supports It
Decree 356 (PDPL Implementation)
See Incident Operations in Action
Ready to see how Incident Operations works with your compliance workflows? Request a personalized demo.
People Also Ask
Playbook-to-notification linkage means that when a playbook reaches the breach confirmation step, the notification lifecycle in the Incident Response module is triggered automatically. This eliminates the manual handoff between the response team and the notification team, ensuring regulatory filing begins immediately upon breach determination.
Yes. While PDPL SLA defaults (72-hour and 360-hour) are pre-configured, every SLA definition is configurable. Organizations can define custom response time targets for any applicable framework or internal policy, and those targets are applied automatically based on incident classification.
The evidence chain tracks every piece of evidence with its collection timestamp, the identity of who collected it, and any custody transfers. Records are tamper-evident, meaning any modification is detectable. The chain is maintained throughout the incident lifecycle and is included in the post-incident review package.
The dashboard provides a single view of team assignments, SLA clocks, and escalation status across all active incidents. Operations leads can see which teams are assigned to which incidents, which SLAs are closest to expiry, and which incidents have triggered escalation, allowing them to prioritize attention and resources in real time.
Yes. The vendor coordination feature tracks vendor acknowledgment, response actions, and evidence submissions within the same incident workflow. When a third-party system is involved in an incident, the vendor's response activities are tracked alongside the internal response, maintaining a single unified record.
Next Steps
Explore the module architecture, then speak with us about the workflows your organization needs to operationalize first.

Start a Compliance Pilot
Test playbook execution, SLA tracking, and evidence chain of custody with a real incident scenario.

Discuss Your Compliance Needs
Walk through your incident response requirements and see how playbook automation fits your operations.









