DPO Radio
Vendor and Third-Party Management
![]() VENDOR AND THIRD-PARTY MANAGEMENT
VENDOR AND THIRD-PARTY MANAGEMENT
Full Vendor Lifecycle Oversight – Onboarding Through Offboarding
Two modules that manage every stage of your vendor relationships: governance handles the lifecycle, risk handles ongoing monitoring.


Why Vendor and Third-Party Management Matters
Vendors process personal data on your behalf, making them a direct extension of your compliance posture. Vietnam's PDPL and Decree 356 require organizations to maintain oversight of sub-processors and cross-border data transfers – obligations that do not end at contract signing. Without structured vendor management, organizations onboard vendors without completing DPA review, skip periodic reassessments, and close vendor relationships without verifying data return or deletion.
The operational risk is concrete: a vendor handling sensitive personal data may change sub-processors without notice, let security certifications lapse, or fail to propagate consent withdrawals. If your vendor oversight depends on calendar reminders and shared folders, these changes go undetected until an audit or incident surfaces them.
ComplianceOne addresses this with two complementary modules. Governance manages the full vendor lifecycle, from structured onboarding with DPA and security assessment review, through periodic review scheduling, to formal offboarding with data deletion verification. Vendor Risk provides continuous monitoring – tracking risk signals, scoring vendors against configurable models, surfacing portfolio-level concentration risks, and routing high-risk vendors through formal risk acceptance with documented rationale. Together, they ensure that every vendor relationship is assessed before activation, monitored during operation, and verified at closure.
Vendor and Third-Party Management Modules
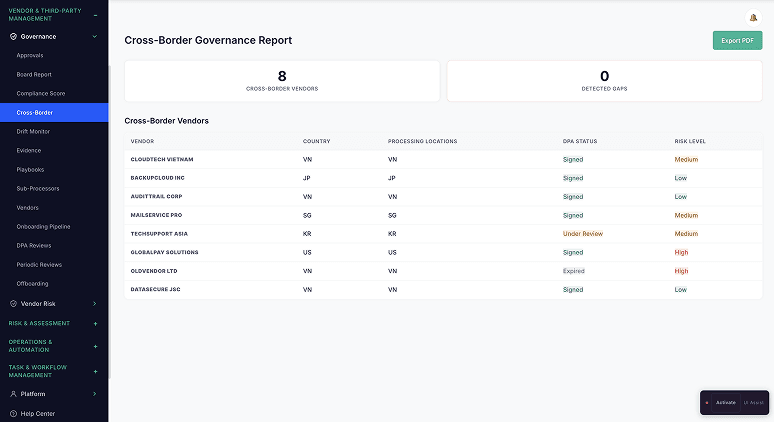
Governance
Full vendor lifecycle – onboarding, DPA review, periodic reviews, offboarding
Manage third-party vendors and sub-processors across their entire lifecycle. Structured onboarding moves vendors through defined stages with DPA review and security assessment sign-off before activation. Periodic review scheduling keeps assessments current with automatic triggers. Drift detection monitors for compliance divergence. Formal offboarding verifies data return or deletion before relationship closure.
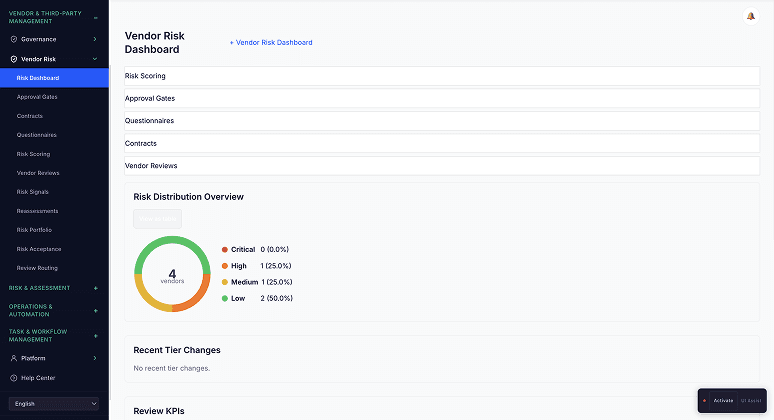
Vendor Risk
Continuous risk monitoring with portfolio analytics and formal risk acceptance
Assess and score vendor risk with configurable scoring models. Continuous risk signal monitoring watches for certificate expiry, assessment gaps, and risk-triggering events, automatically queuing reassessments without manual scheduling. Portfolio analytics provide heat maps, trend lines, and concentration analysis across your entire vendor population. High-risk vendors are routed through a formal risk acceptance workflow with reviewer sign-off and rationale capture.
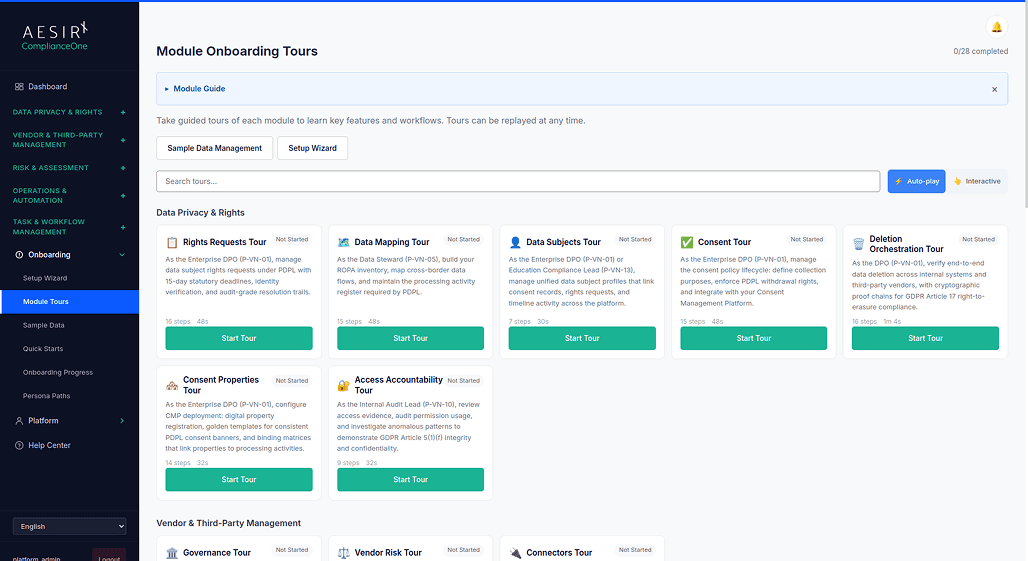
See Vendor and Third-Party Management in Action
Ready to see how ComplianceOne handles vendor onboarding, risk monitoring, and compliance oversight in practice? Request a personalized demo with your vendor scenarios.
Next Steps
Explore the module architecture, then speak with us about the workflows your organization needs to operationalize first

Start a Compliance Pilot
Deploy the Vendor Management modules against your current vendor portfolio. See structured onboarding and risk scoring in action within 30 days.

Discuss Your Compliance Needs
Talk to our team about your vendor oversight requirements, sub-processor obligations, and cross-border transfer compliance needs.
Frequently Asked Questions
Governance manages the lifecycle, when a vendor is onboarded, reviewed, or offboarded. Vendor Risk manages the risk picture – how risky each vendor is, what signals indicate changes, and whether risk has been formally accepted. Governance triggers risk assessments at onboarding and periodic review milestones. Risk monitoring can trigger governance actions when risk signals indicate a vendor needs reassessment outside the normal review cycle.
Both modules are independently configurable. However, they deliver the most value together. Vendor Governance without Vendor Risk means you manage the lifecycle but lack continuous monitoring. Vendor Risk without Vendor Governance means you score risk but lack structured onboarding and offboarding workflows. Most organizations enable both.




