DPO Radio
Consent
Why Consent Matters
Consent is not a one-time checkbox. Under Vietnam's PDPL and the Vietnam Data Law, organizations must maintain verifiable consent records, honor withdrawals promptly, and demonstrate that their deployed consent banners match their documented policies. When consent state diverges across systems, the organization is exposed to regulatory findings it cannot defend.
Enterprise DPOs (P-VN-01) are responsible for ensuring that consent policies are current, approved, and consistently applied. Data Governance Leads (P-VN-05) manage the system-level integration between consent management platforms and internal processing records. Both roles participate in the Consent and Preference Governance workflow (UC-VN-13), which spans all system and channel owners across marketing, CRM, product, and legal teams.
Without a structured consent governance system, policies are version-controlled in documents that no one cross-references against live CMP configurations. Withdrawal requests are processed manually with no confirmation that downstream systems have stopped processing. Sensitive data consent, which requires enhanced review before activation, is handled through the same informal process as standard consent. When an auditor asks for proof that consent state across systems is consistent, the answer is a best-effort reconstruction.
Consent centralizes policy management with version control, links consent purposes to legal bases and processing activities, and maintains bidirectional synchronization with AesirX CMP Pro. Drift detection alerts when deployed banners diverge from approved policies, and a mismatch reconciliation workflow resolves discrepancies through a structured process rather than ad-hoc fixes.
How It Works
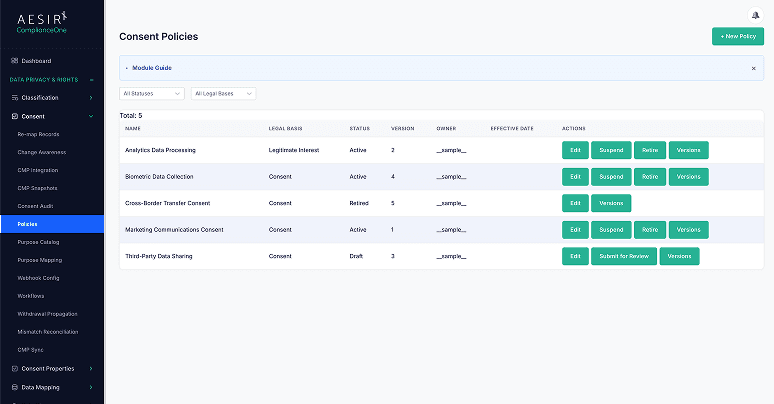
Consent Policies
Version-controlled consent policy records with approval workflows. Each policy captures its scope, purposes, legal basis, and effective dates. Changes route through review and approval before taking effect.
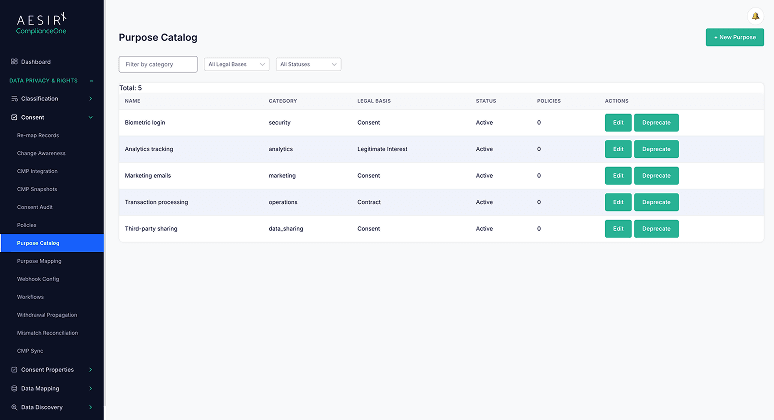
Purpose Catalog
Link consent purposes to legal bases and processing activities. The catalog provides a single reference for what each consent purpose covers, why it exists, and which processing activities depend on it.
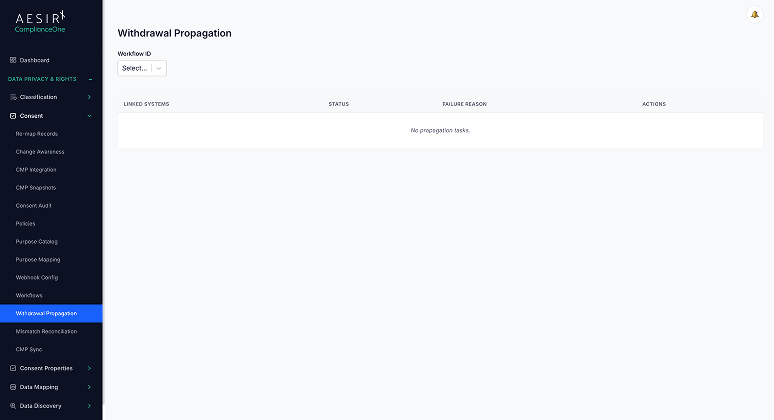
Withdrawal Propagation Tracking
Track consent withdrawals as they flow downstream across connected systems. Each withdrawal is monitored until all receiving systems confirm they have stopped the relevant processing, creating a documented propagation chain.
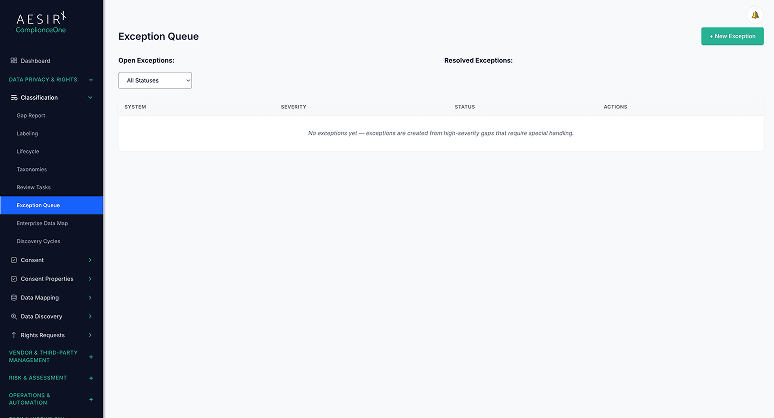
CMP Enforcement and Drift Detection
Monitor deployed consent banners against approved policies. Drift detection alerts when CMP configuration diverges from the documented policy — whether through unauthorized changes, deployment errors, or version mismatches.
Sensitive Data Consent Policies
An enhanced review gate for high-risk processing categories requires additional approver sign-off before activation. This ensures that consent policies governing sensitive personal data receive the scrutiny their risk level demands.
Mismatch Reconciliation Workflow
When discrepancies are identified between internal consent records and live CMP state, a structured reconciliation process routes each mismatch to the appropriate owner for resolution. This replaces ad-hoc fixes with documented, auditable corrections.
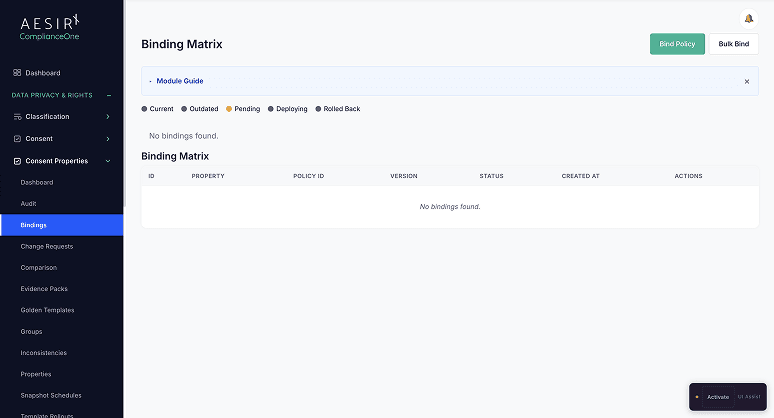
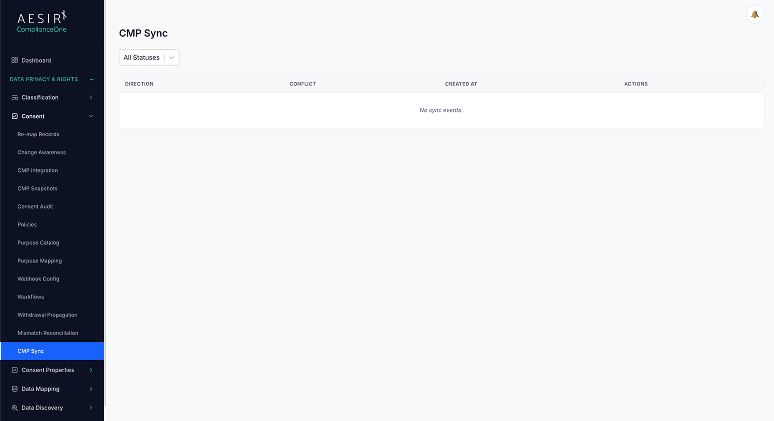
Bidirectional CMP Synchronization
Two-way sync with AesirX CMP Pro keeps internal policy records and deployed CMP configurations aligned. Automatic conflict detection identifies when both sides have changed, and resolution routing ensures conflicts are handled by the right team.
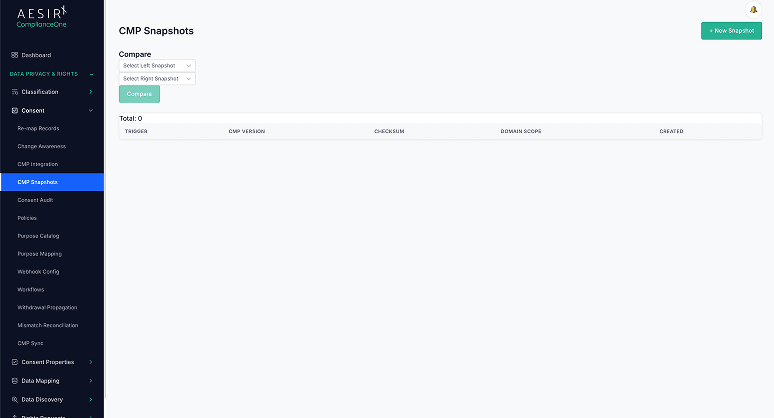
Snapshot History
Point-in-time snapshots of consent configurations preserve the state of policies and CMP settings at any given moment. Snapshots support audit inquiries that ask "what was the consent configuration on date X?"
The Difference

Without Consent
With Consent
Built for Real Compliance Operations
Bidirectional CMP synchronization maintains alignment between internal policy records and deployed consent banners, with automatic conflict detection when both sides change independently.
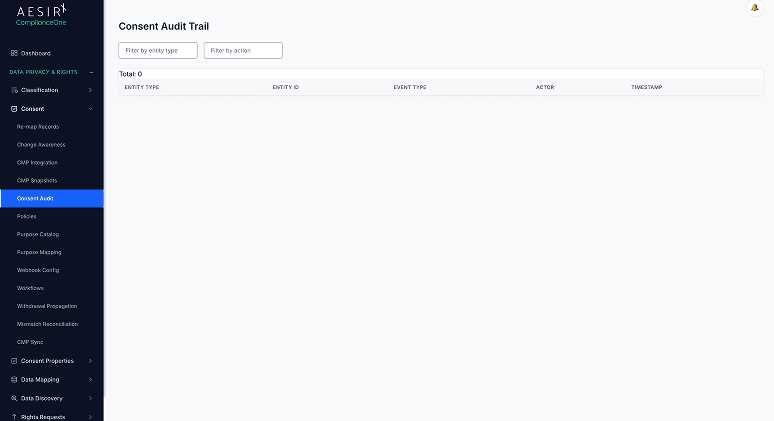
Withdrawal propagation tracking follows each withdrawal downstream until every connected system confirms it has stopped the relevant processing, creating the evidence chain regulators require.
Point-in-time consent configuration snapshots answer the audit question "what was deployed on this date?" without reconstruction from logs or memory.
Regulatory Framework Support
Framework
How Consent Supports It
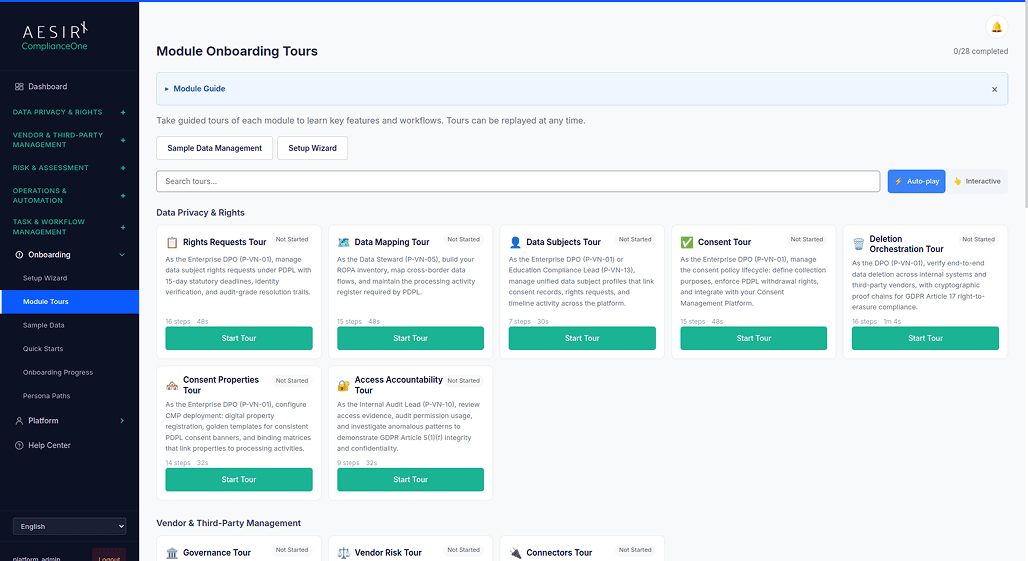
See Consent in Action
Ready to see how Governance works with your compliance workflows? Request a personalized demo.
People Also Ask
Drift detection continuously compares the live CMP configuration against the approved policy records in the system. When a divergence is identified – whether from unauthorized changes, deployment errors, or version mismatches – an alert is raised for the responsible team to investigate.
The withdrawal is recorded and tracked as it propagates to all connected downstream systems. Each system must confirm receipt and cessation of the relevant processing. The propagation chain is documented in the audit trail as evidence of timely compliance.
Consent policies governing high-risk processing categories ( such as health data, biometric data, or financial records) route through an enhanced review gate requiring additional approver sign-off before the policy is activated. This gate is configurable based on the organization's classification.
The module provides bidirectional synchronization with AesirX CMP Pro. Two-way sync keeps internal policy records and deployed configurations aligned, with automatic conflict detection and resolution routing when both sides change independently.
The snapshot history feature captures point-in-time records of consent configurations. Auditors can review the exact policy state, CMP configuration, and purpose catalog as they existed on any given date without relying on log reconstruction.
Next Steps
Explore the module architecture, then speak with us about the workflows your organization needs to operationalize first.

Start a Compliance Pilot
Test Consent with your actual policies, CMP integration, and withdrawal workflows.

Discuss Your Compliance Needs
Walk through your consent architecture, CMP setup, and cross-system synchronization requirements.









