DPO Radio
AesirX Incident Response
Why Incidents Matters
Data breaches trigger strict regulatory obligations under Vietnam's Personal Data Protection Law (PDPL). Organizations must notify the Ministry of Public Security within 72 hours of breach discovery, submit supplementary reports within 360 hours, and maintain records of every disclosure for regulatory inspection. Missing any deadline or losing evidence during the response process exposes the organization to enforcement action.
Breach Response Leads (P-VN-09) are responsible for orchestrating the entire notification lifecycle, from initial detection through remediation and formal closure. In practice, this means coordinating security operations, legal, IT, and department data owners simultaneously while regulatory clocks are ticking. Without a structured system, critical handoffs are missed, evidence is scattered across email threads, and supplement submissions slip past deadlines.
Organizations that rely on spreadsheets and email for incident response face a consistent set of failures: incomplete breach assessments because intake forms capture inconsistent details, remediation tasks that stall because no one owns them, and disclosure registers that do not exist until an inspector asks for one. The result is a reactive, disorganized response that increases both regulatory risk and operational cost.
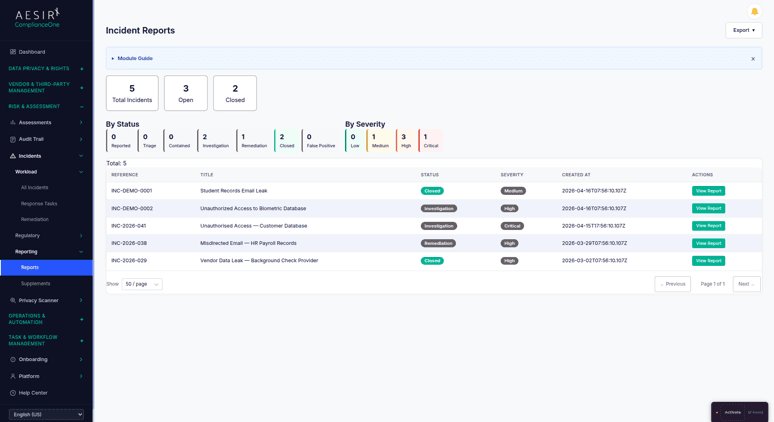
AesirX ComplianceOne Incident Response provides a complete breach notification lifecycle – structured intake, triage and classification, breach assessment with notification determination, MPS filing with supplement loop tracking, multi-department remediation coordination with sign-off gates, authority request handling, and a maintained disclosure register. Security operations teams, legal counsel, IT departments, and department data owners all work within the same system, with every action logged to an immutable timeline.
How It Works
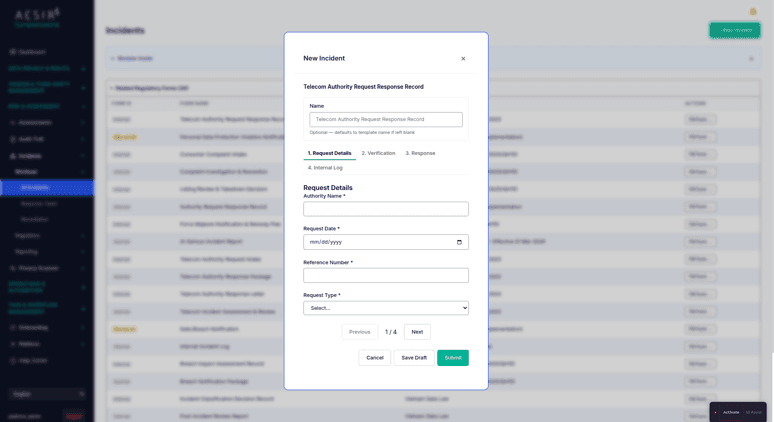
Incident Intake
A structured intake form captures all essential incident details at the point of detection – what happened, when it was discovered, which systems and data subjects are affected, and who reported it. Standardized intake ensures no critical information is missed during the initial high-pressure response window.
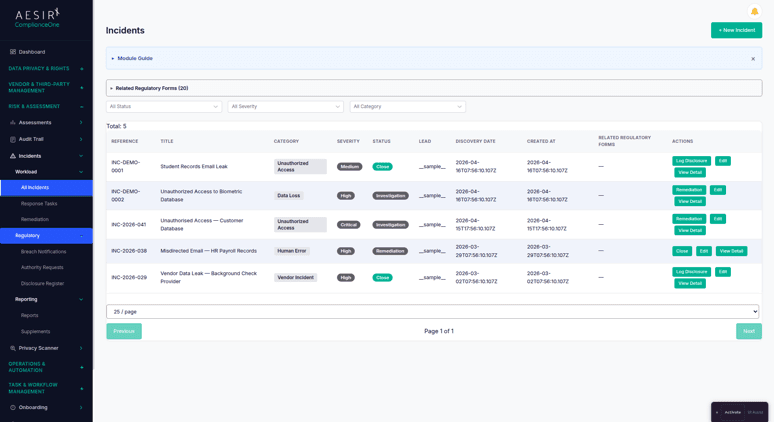
Triage and Classification
Every incident is scored for severity and assessed for breach determination. The triage process applies consistent criteria to determine whether an incident constitutes a reportable data breach, driving the correct downstream workflow – notification for confirmed breaches, monitoring for near-misses.
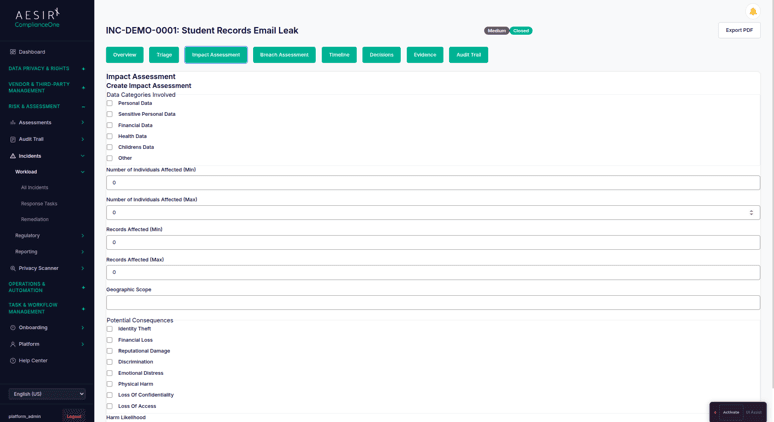
Breach Assessment
For confirmed breaches, a structured assessment captures the impact analysis: categories of personal data affected, number of data subjects, notification requirements under applicable frameworks, and risk to individuals. This assessment feeds directly into the notification workflow.
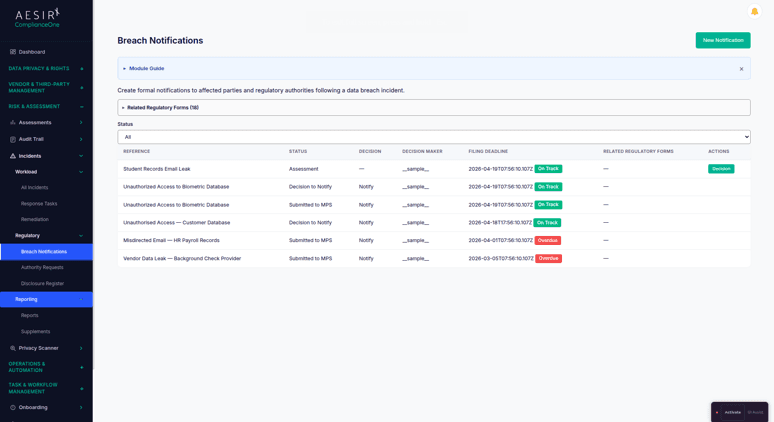
Breach Notification Lifecycle
The end-to-end notification workflow covers initial MPS notification (within 72 hours under PDPL), supplement submissions (within 360 hours), and formal case closure. Each stage has its own deadline tracker, required fields, and approval gates. The system tracks where each notification stands and what remains outstanding.
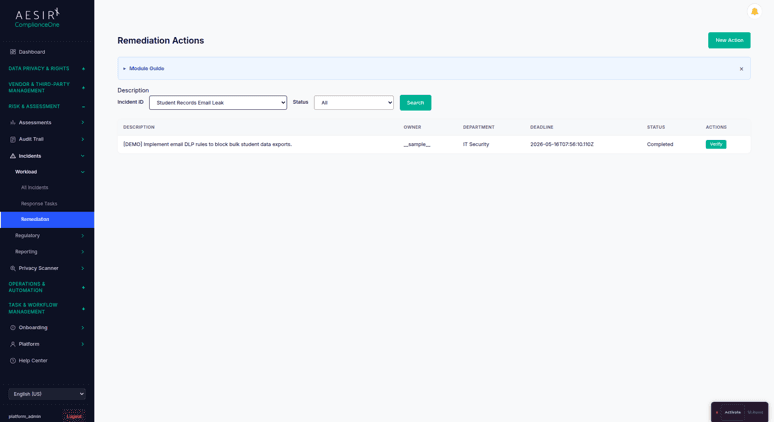
Multi-Department Remediation Coordination
Remediation tasks are assigned across departments – security operations for containment, IT for system hardening, legal for regulatory filings, department owners for process corrections. Each department's progress is tracked with consolidated status and sign-off gates that prevent premature closure.
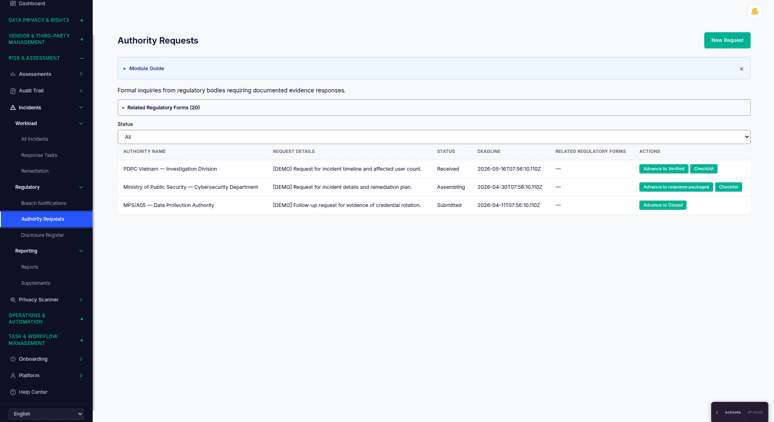
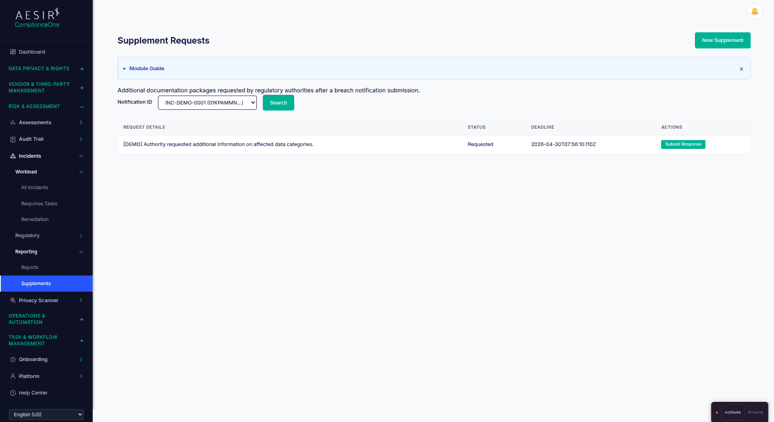
Authority Request Handling
A dedicated workflow manages PDPL and NIS regulatory inquiries. When authorities request additional information, the system packages the relevant evidence, tracks the submission, and maintains a record of every exchange.
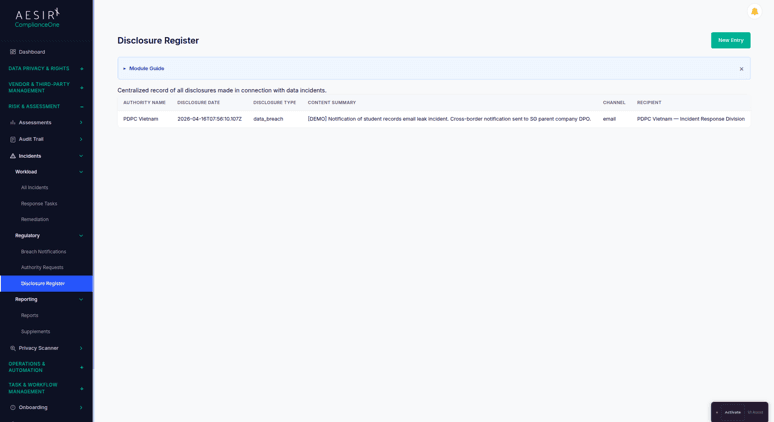
Disclosure Register
A maintained register of all breach notifications and regulatory disclosures provides a single source of truth for inspection readiness. Every notification, supplement, authority exchange, and closure is recorded with dates, recipients, and supporting evidence.
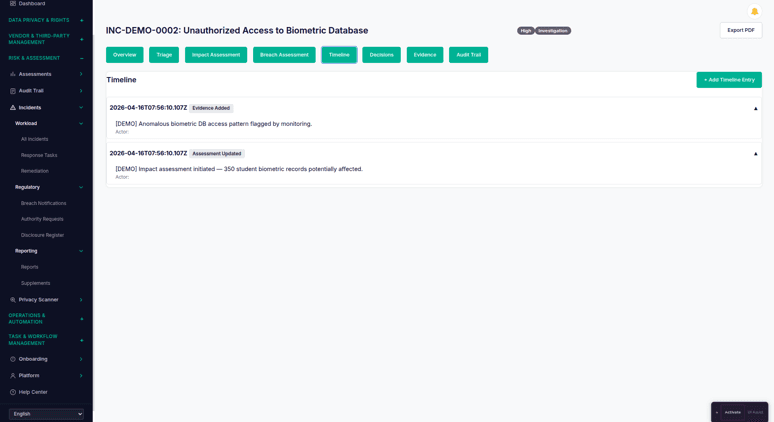
Timeline and Decision Log
An immutable chronological record captures every action and decision throughout the incident lifecycle. This log serves as both an operational coordination tool and an audit artifact – every triage decision, task assignment, notification submission, and sign-off is recorded with timestamps and contributor identity.
Supplement Flow
When MPS requests additional information, a team member manually initiates the supplement workflow, routes the request to the relevant departments to collect the required updates, and resubmits through the MPS portal, all tracked within the same filing case to preserve the complete history and lineage.
Regulatory Deadline Timers
Color-coded countdown badges on each filing case show which submissions are on track, approaching their deadline, or at risk. Timers are visible to all stakeholders so urgency is clear without requiring manual status checks.
Compare the Difference

Without Incidents

With Incidents
Built for Real Compliance Operations
Full breach notification lifecycle coverage, from structured intake through MPS filing, supplement submission, and formal closure, in a single module with no manual handoffs between stages.
Multi-department remediation coordination with individual sign-off gates ensures no department's tasks are overlooked and no incident is prematurely closed.
Integrated with the platform's unified audit system, every incident action is recorded with contributor identity and timestamp, providing a complete evidence chain for regulatory inspection.
Regulatory Framework Support
Framework
How Incident Response Supports It
Decree 356 (PDPL Implementation)
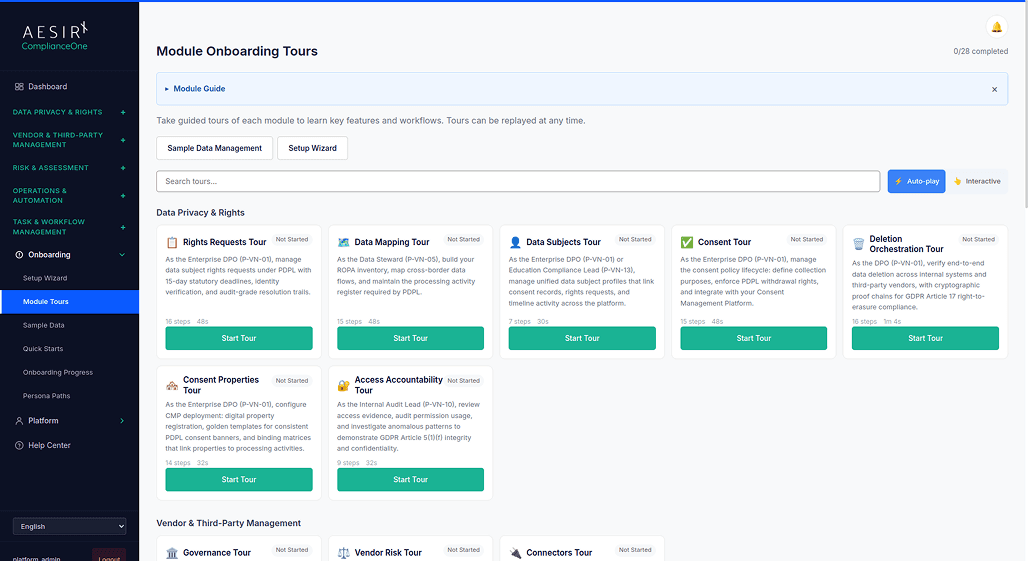
See Incidents in Action
Ready to see how Incident Response works with your compliance workflows? Request a personalized demo.
People Also Ask
The breach notification lifecycle tracks the 72-hour window from the moment of breach confirmation. Each notification stage (initial filing, supplement, and closure) has its own deadline tracker and required fields, so the responsible team always knows what is due and when.
Yes. Multi-department remediation coordination allows tasks to be assigned to security operations, legal, IT, and department data owners in parallel. Each department's progress is tracked independently with consolidated status visible to the Breach Response Lead, and sign-off gates prevent closure until all departments confirm completion.
The authority request handling workflow manages incoming regulatory inquiries. It packages the relevant evidence from the incident record, tracks the submission, and maintains a complete log of every exchange with the authority, all linked to the original incident case.
Yes. Every notification submission, supplement filing, authority exchange, and closure is automatically recorded in the Disclosure Register with dates, recipients, and supporting evidence. The register is always current and ready for inspection without manual compilation.
Incident Response works within the platform's unified audit system. Incidents can be linked to related records across the platform – vendor coordination, data mapping entries, and compliance assessments. The immutable timeline and evidence packs support cross-module audit trails.
Next Steps
Explore the module architecture, then speak with us about the workflows your organization needs to operationalize first.

Start a Compliance Pilot
Test the full breach notification lifecycle with your team – intake, triage, notification, and remediation.

Discuss Your Compliance Needs
Talk through your incident response requirements and see how the platform fits your regulatory obligations.









