DPO Radio
AesirX Vendor Risk
Why Vendor Risk Matters
Organizations rely on external vendors for critical services, but every vendor relationship introduces risk; data exposure, service disruption, regulatory non-compliance. Under the Vietnam PDPL and Cybersecurity Law, organizations must demonstrate ongoing oversight of third parties processing personal data or operating within critical information systems. A point-in-time vendor assessment completed at onboarding does not satisfy this obligation.
Cross-Border Transfer and Vendor Governance Leads (P-VN-08) manage vendor portfolios that may span dozens of relationships, each with different risk profiles, contract timelines, and regulatory exposure. When risk assessments live in static documents, they become stale the moment a vendor's circumstances change – a certificate expires, a sub-processor is added, or a security incident is reported.
Without continuous monitoring, the organization's risk picture degrades silently. High-risk vendors continue operating without formal acceptance. Assessment gaps accumulate without anyone noticing. Portfolio-level risk concentrations (too many critical vendors in one jurisdiction, too many vendors with expiring contracts) remain invisible until an audit forces the analysis.
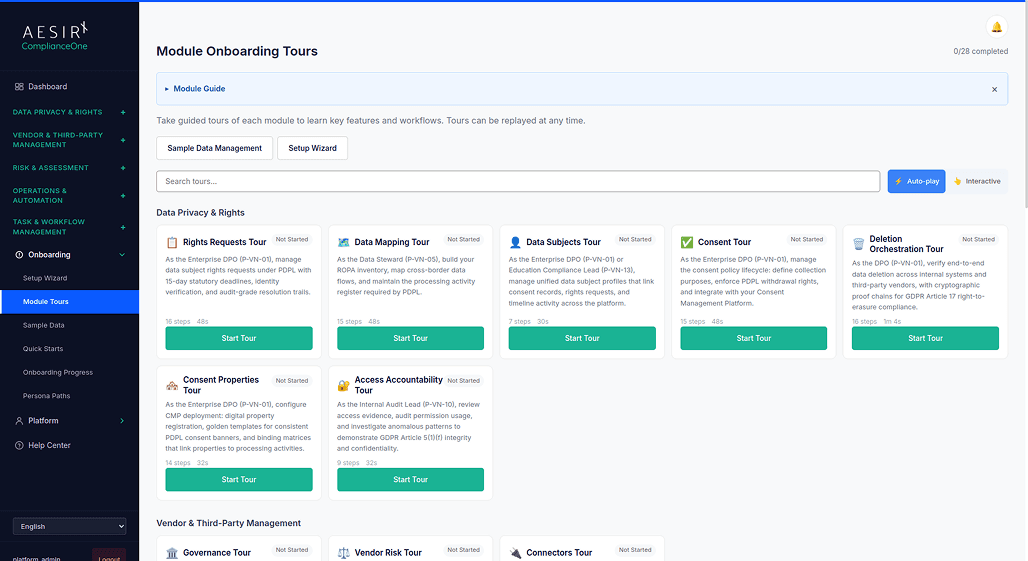
Vendor Risk solves this with configurable scoring models, structured due diligence questionnaires, procurement gates that prevent unapproved vendors from advancing, and continuous risk signal monitoring that queues reassessments automatically when conditions change. Risk portfolio analytics provide a cross-vendor aggregate view with heat maps and trend analysis, while a formal risk acceptance workflow ensures high-risk decisions are documented with reviewer sign-off. The module supports vendor onboarding, third-party risk, and change impact review workflows used by procurement, IT security, legal, and department owners.
How It Works
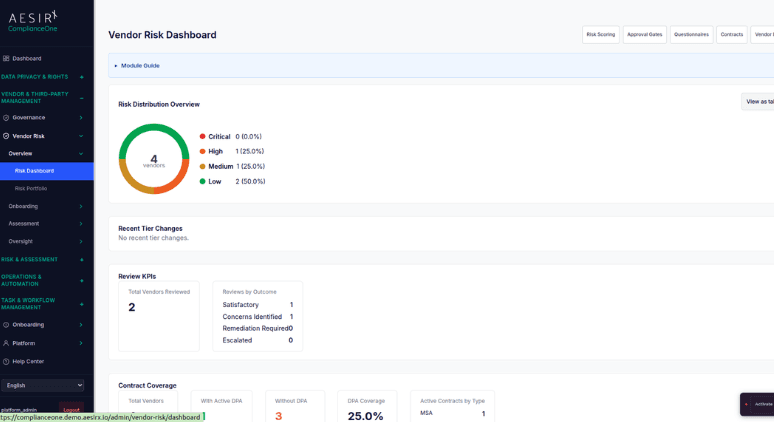
Risk Dashboard
A visual overview of the vendor risk landscape showing risk distribution, trend direction, and vendors requiring immediate attention. The dashboard surfaces the most urgent risk items so teams can act on what matters first.
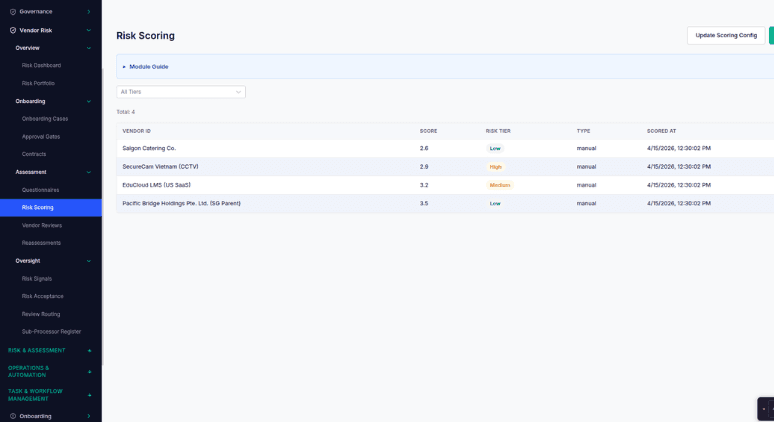
Scoring Models
Configurable risk scoring frameworks that define how vendor risk is calculated. Organizations can tailor scoring criteria to their specific risk appetite and regulatory requirements, ensuring scores reflect what actually matters to the business.
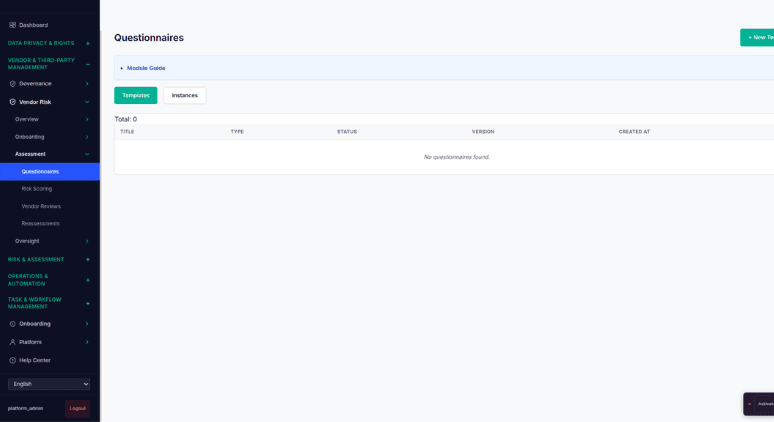
Due Diligence Questionnaires
Structured assessment questionnaires sent to vendors as part of the evaluation process. Responses feed directly into the scoring model, eliminating manual data entry and ensuring consistent evaluation across all vendors.
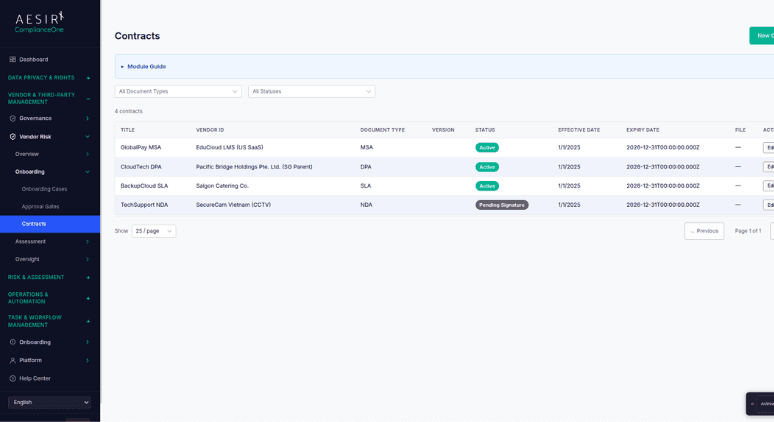
Contract Tracking
Monitor contract terms, renewal dates, and key clauses across all vendor relationships. Expiring contracts and missing terms are surfaced proactively so procurement and legal teams can act before deadlines pass.
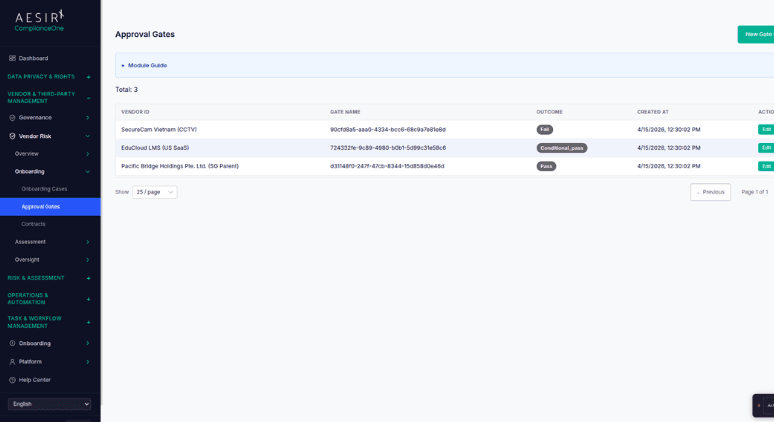
Procurement Gates
Approval checkpoints that prevent new vendors from being onboarded until risk assessment requirements are satisfied. Gates ensure that no vendor begins processing data without a completed evaluation and appropriate sign-off.
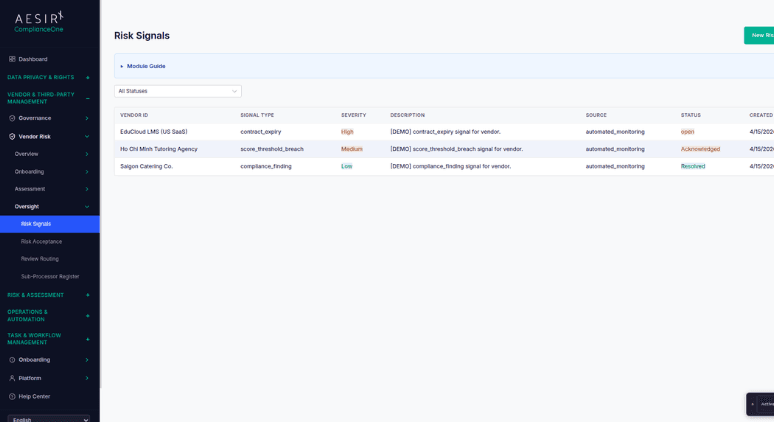
Continuous Risk Signal Monitoring
Monitor vendors for risk-triggering events; news alerts, certificate expiry, assessment gaps, or changes in sub-processor arrangements. When a signal is detected, the module automatically queues a reassessment without requiring manual scheduling.
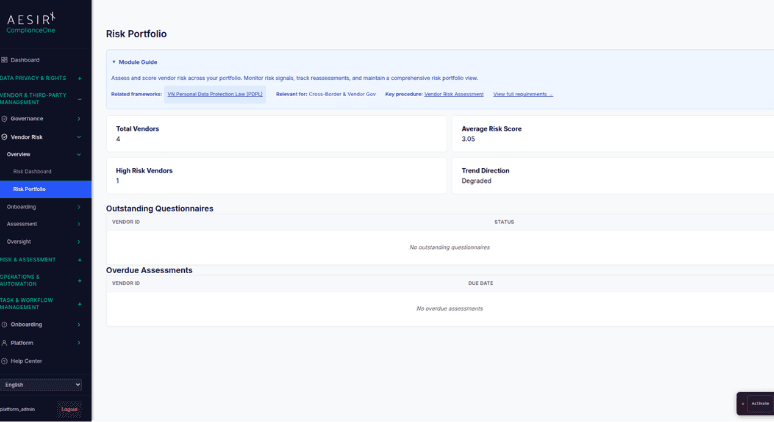
Risk Portfolio Analytics
An aggregate view across the entire vendor population with heat maps, trend lines, and concentration analysis. Leadership can see where risk is concentrated (by jurisdiction, by service type, by contract value) and make informed decisions about the portfolio.
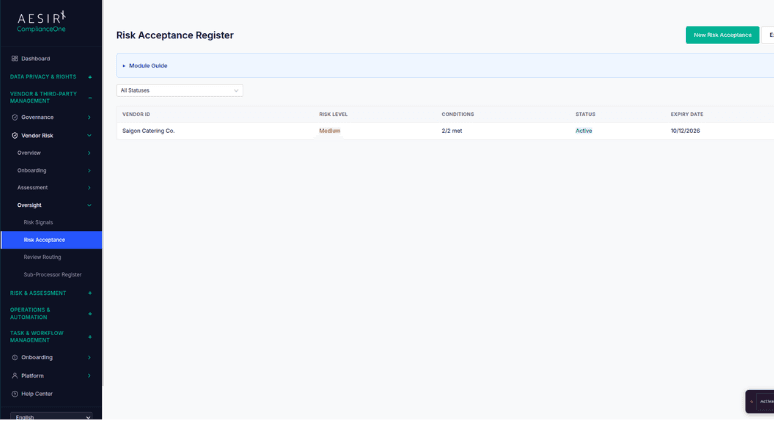
Formal Risk Acceptance Workflow
When a vendor's risk score exceeds the organization's threshold, the formal risk acceptance workflow routes the decision through a documented process. Reviewers record their rationale and sign off, creating an auditable record that the risk was knowingly accepted rather than overlooked.
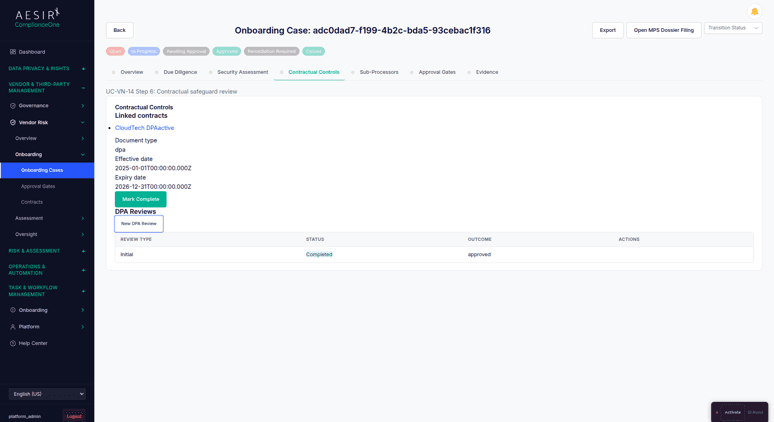
DPA Review and Security Assessment Workflows
Route Data Processing Agreements and security questionnaires through structured review and sign-off before a vendor is activated. Reviewers see exactly what needs their attention, and sign-off is recorded for audit purposes.
Compare the Difference

Without Vendor Risk

With Vendor Risk
Built for Real Compliance Operations
Continuous risk signal monitoring and automated reassessment keep vendor evaluations current without requiring manual scheduling – when a certificate expires or an assessment gap is detected, the module acts.
Risk portfolio analytics aggregate risk data across the entire vendor population into heat maps and trend lines, giving leadership the cross-vendor visibility needed for informed decision-making.
The formal risk acceptance workflow creates an auditable record of every high-risk vendor decision, with reviewer rationale and sign-off captured for regulatory inspection.
Regulatory Framework Support
Framework
How Vendor Risk Supports It
Decree 356 – PDPL Implementation
See Vendor Risk in Action
Ready to see how Vendor Risk works with your compliance workflows? Request a personalized demo.
People Also Ask
Periodic reviews run on a fixed schedule. Continuous monitoring watches for risk-triggering events (certificate expiry, news alerts, assessment gaps) between scheduled reviews and automatically queues a reassessment when something changes. The two approaches complement each other.
Yes. Scoring models are configurable so organizations can define the criteria, weights, and thresholds that reflect their specific risk appetite and regulatory requirements.
When a vendor's risk exceeds the organization's threshold, the workflow routes the decision to designated reviewers. Each reviewer records their rationale and signs off. The complete decision record (risk score, rationale, reviewer identity, and timestamp) is stored for audit purposes.
Portfolio analytics aggregate risk scores across all vendors and present them as heat maps, trend lines, and concentration views. This makes it possible to identify patterns, such as too many high-risk vendors in a single jurisdiction, that are invisible when vendors are evaluated individually.
Procurement gates act as approval checkpoints. A vendor cannot advance past the gate until the required risk assessment is completed and the appropriate sign-off is obtained. This prevents vendors from beginning data processing before evaluation is finished.
Next Steps
Explore the module architecture, then speak with us about the workflows your organization needs to operationalize first.

Start a Compliance Pilot
Test Vendor Risk with your actual vendor portfolio – scoring, monitoring, and portfolio analytics included.

Discuss Your Compliance Needs
Walk through your vendor risk management requirements and see how the module fits your program.









