DPO Radio
AesirX Access Accountability
Why Access Accountability Matters
Access to sensitive data is one of the highest-risk areas in any compliance program. Under the Vietnam PDPL and Cybersecurity Law, organizations must demonstrate that access to personal data and critical systems is controlled, justified, periodically reviewed, and auditable. A permissions matrix alone does not satisfy this. Regulators expect evidence of active oversight: who accessed what, why, whether that access was reviewed, and what happened when anomalies were detected.
Cybersecurity and Legal Operations Leads (P-VN-06) manage access policies across systems that process sensitive and personal data. Internal Audit and Regulatory Inspection Leads (P-VN-10) must present evidence that access controls are not just configured but actively enforced and periodically certified. When access accountability is managed through manual reviews and disconnected logs, gaps accumulate: access entitlements drift beyond what is justified, suspicious access patterns go uninvestigated, and evidence for regulatory inspections must be assembled from multiple sources under time pressure.
Without structured access accountability, the organization cannot demonstrate a closed loop – from policy definition, through periodic review, to investigation and remediation of violations. Access review campaigns are ad hoc or overdue. Investigation findings are documented informally without linking to remediation actions. When a regulator requests an evidence package, the team spends days assembling logs, certifications, and investigation records from different systems.
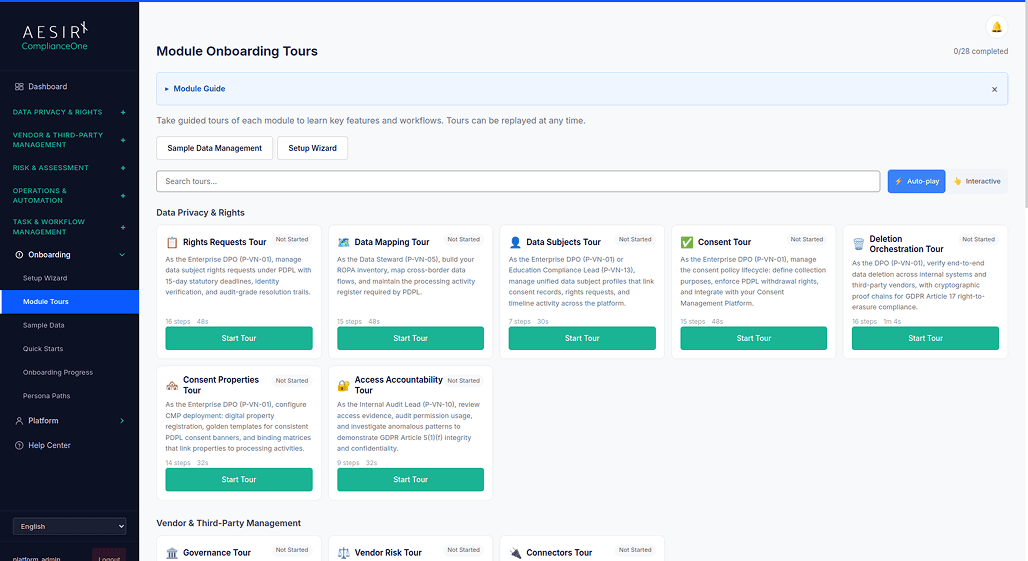
Access Accountability addresses these challenges with framework-linked access policies that attach directly to regulatory frameworks, periodic review campaigns where reviewers certify or revoke each entitlement, investigation workflows that connect findings to remediation tasks and support evidence packaging for authority submissions, session monitoring and access logging at the record level, justification requirements for sensitive data access, and per-framework audit evidence package generation. The module supports Cybersecurity Incident Response and Authority Cooperation (UC-VN-05), Cross-Framework Regulator Inspection and Internal Audit Evidence Pack (UC-VN-09), and Current-State Assessment (UC-VN-16) workflows.
How It Works
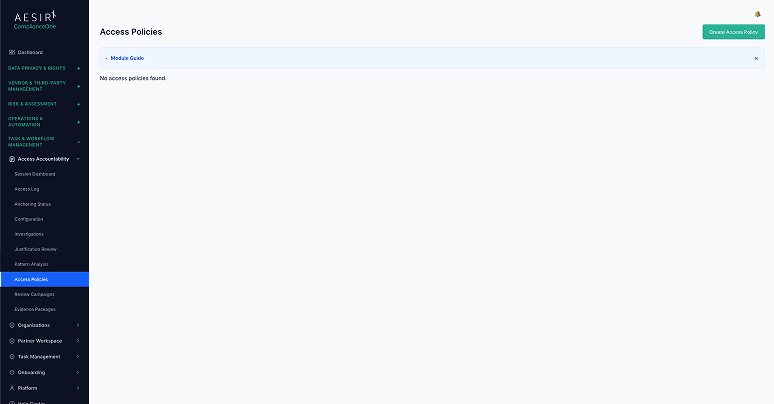
Framework-Linked Access Policies
Attach access control policies directly to regulatory frameworks with configurable review frequency and a status lifecycle (draft, active, under review, retired). Each policy records which framework it supports and when it was last reviewed, ensuring access controls are grounded in actual regulatory obligations.
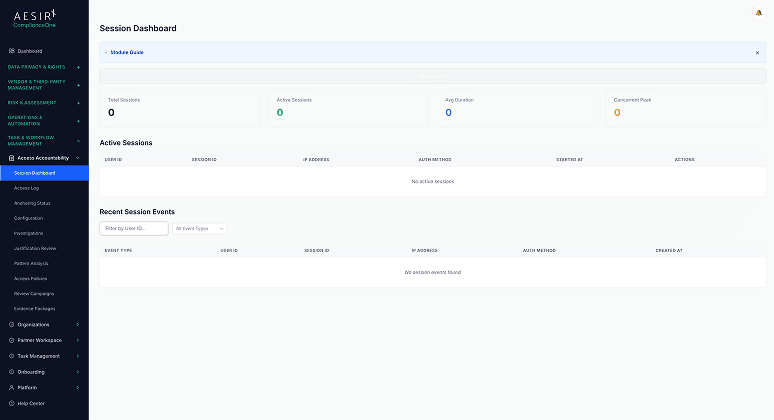
Session Monitoring
Track user login sessions across the platform. The session dashboard shows active sessions, session history, and session metadata – providing visibility into who is accessing the system and when.
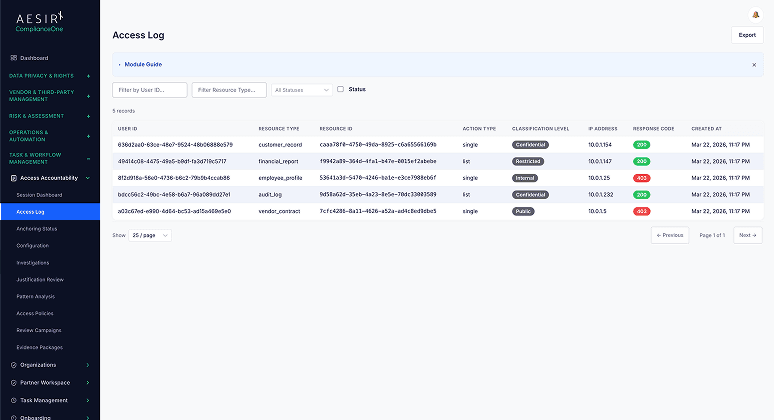
Access Logging
Record-level access tracking that captures which records were accessed, by whom, and when. Access logs provide the granular evidence needed to demonstrate that sensitive data access is monitored and attributable.
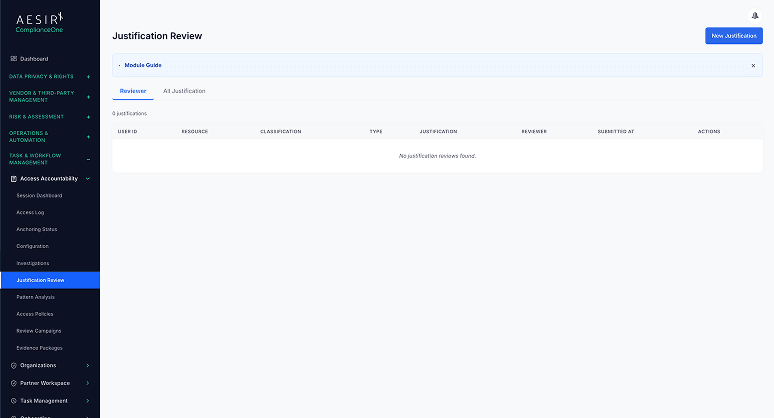
Justification Requirements
Require users to provide a justification before accessing sensitive data. Justifications are recorded alongside the access event, creating an auditable record that access was purposeful rather than incidental. A dedicated justification review view surfaces pending and completed justifications for compliance oversight.
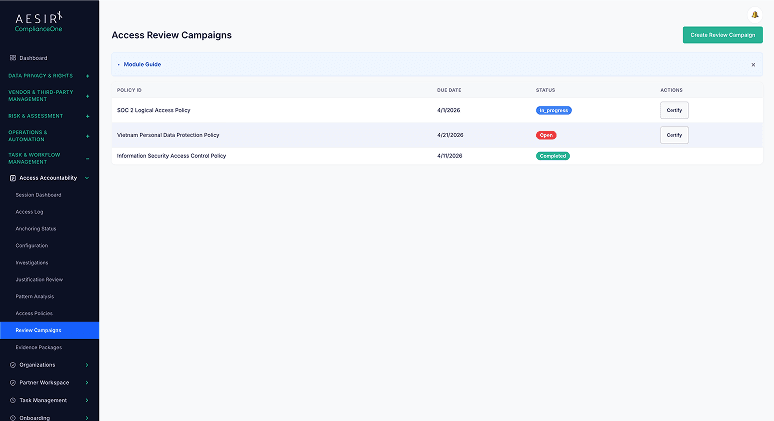
Periodic Review Campaigns with Certification
Launch structured access certification campaigns where reviewers evaluate each access entitlement and certify or revoke it. Campaign results – who was certified, who was revoked, who reviewed – are captured for audit purposes, demonstrating that access entitlements are periodically validated.
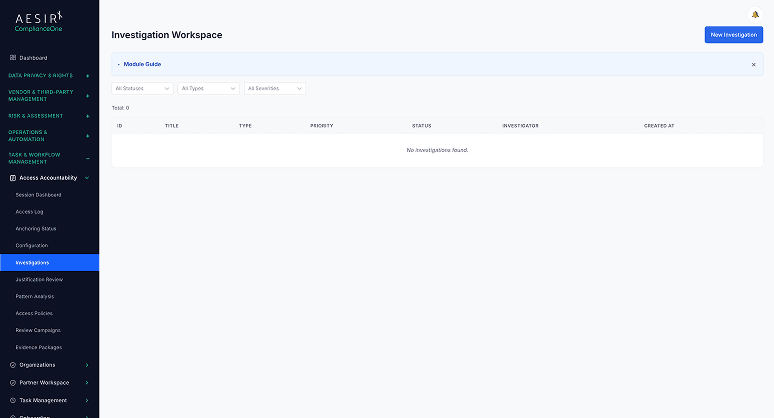
Investigation Workflows with Remediation Linking
A formal investigation process for suspected access misuse. Investigations connect findings to remediation tasks and support packaging evidence for authority submissions. The complete chain (detection, investigation, finding, remediation) is maintained in a single workflow.
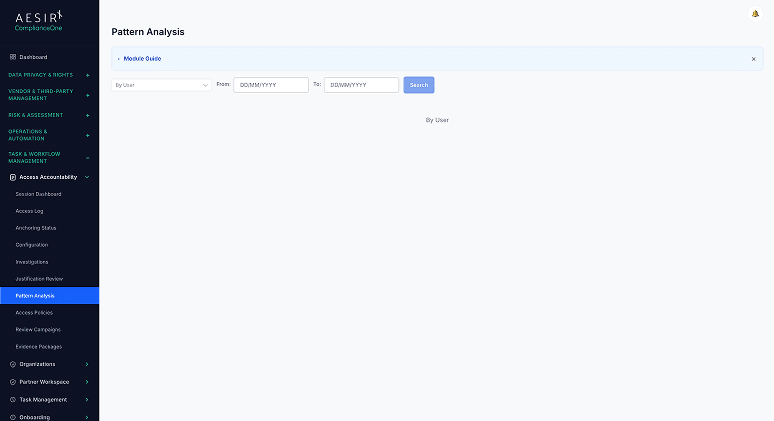
Pattern Analysis
Detect unusual access patterns across users and systems. Pattern analysis surfaces anomalies (unexpected access times, unusual data volumes, access to records outside a user's normal scope) that may warrant investigation.
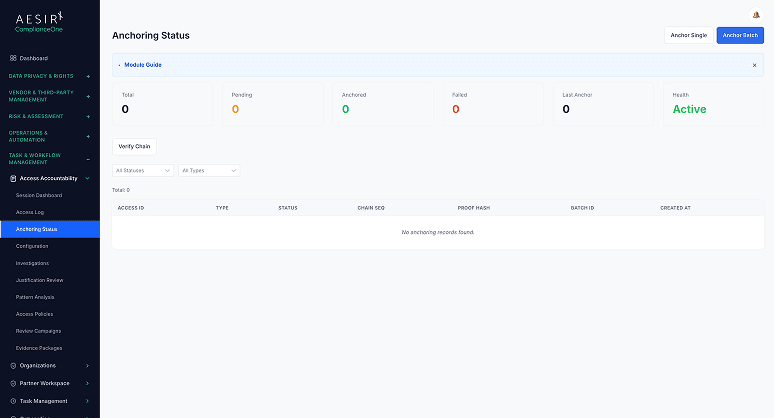
Cryptographic Anchoring
Tamper-proof access event records using cryptographic anchoring. This provides assurance that access logs have not been altered after the fact – a requirement for evidence integrity in regulatory submissions.
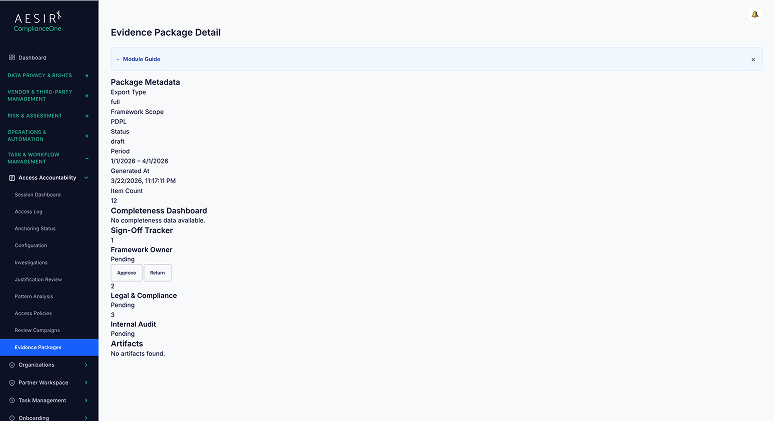
Audit Evidence Package Generation
Compile per-framework evidence packages containing access logs, certification campaign results, investigation outcomes, and policy documentation. Packages are formatted for regulatory inspection so the team is not assembling evidence under time pressure when an auditor arrives.
Compare the Difference

Without Access Accountability

With Access Accountability
Built for Real Compliance Operations
Framework-linked access policies with lifecycle management (draft, active, under review, retired) ensure that every access control maps to a specific regulatory obligation, eliminating the gap between documented policy and actual enforcement.
Periodic review campaigns with certification capture reviewer decisions for every access entitlement, creating the structured evidence of active oversight that regulators expect during inspections.
Per-framework audit evidence package generation compiles access logs, certifications, investigation outcomes, and policy records into inspection-ready bundles, so the team is prepared before an auditor requests documentation rather than assembling it after.
Regulatory Framework Support
Framework
How Access Accountability Supports It
Decree 356 — PDPL Implementation
See Access Accountability in Action
Ready to see how Access Accountability works with your compliance workflows? Request a personalized demo.
People Also Ask
You launch a certification campaign that assigns reviewers to evaluate specific access entitlements. Each reviewer certifies that the access is still appropriate or revokes it. The campaign results – every decision, reviewer identity, and timestamp – are captured and stored for audit purposes.
Yes. A single access policy can be linked to one or more frameworks. Each linkage records the specific regulatory obligation the policy supports, and the review frequency can be configured per framework to meet different regulatory cadences.
The investigation workflow handles suspected access misuse from detection through resolution. It captures the investigation details, findings, and recommended actions, then links findings to remediation tasks. The complete investigation record can be packaged as evidence for authority submissions.
Evidence packages are compiled per framework and include access logs, certification campaign results, investigation outcomes, and policy documentation. Packages are assembled within the module and formatted for regulatory inspection, ready to present when an auditor requests documentation.
Cryptographic anchoring creates tamper-proof records of access events. Each event is anchored so that any subsequent modification would be detectable. This provides assurance of evidence integrity, which is important when access logs are submitted to regulatory authorities as proof of compliance.
Next Steps
Explore the module architecture, then speak with us about the workflows your organization needs to operationalize first.

Start a Compliance Pilot
Test Access Accountability with your real access policies – review campaigns, investigations, and evidence packaging included.

Discuss Your Compliance Needs
Walk through your access oversight requirements and see how the module fits your regulatory compliance program.









