Most organizations believe they are operationally compliant because they have policies, checklists, and a team that responds when auditors ask questions. But responding to an auditor is not the same as being ready for one. Operational compliance means your daily work produces the evidence, contributor records, and submission-ready documentation that regulators and auditors require – without a separate scramble to assemble it after the fact.
The difference is not philosophical. It is the difference between a DPO who can see every DPIA filing across the organization – who is contributing, what is missing, what is overdue – and one who spends the first two weeks of every audit cycle chasing department heads for inputs that should have been captured months ago.
The Problem: Evidence as Afterthought
Ask a compliance manager where the evidence for last quarter's regulatory filings lives. In most organizations, the answer involves some combination of shared drives, email threads, spreadsheet trackers, and a folder structure that made sense to whoever created it.
This is not operational compliance. This is a documentation project that runs in parallel to actual compliance work, and it breaks in predictable ways. Department contributions arrive in inconsistent formats. Version control is manual and unreliable. When a filing deadline arrives, the team assembles a dossier from scattered sources, hoping nothing was missed or overwritten. There is no single source of truth for filing status. There is no reliable way to answer "who contributed what, and when was it last reviewed?"
The accountability gaps are concrete. An annual attestation pack should be generated from current approved records, not from manual cut-and-paste across departmental submissions that may not reflect the latest state. When responsibility assignments exist only in a project management tool disconnected from the compliance record, the question of who is accountable for a specific regulatory obligation becomes a conversation instead of an immediate lookup.
In practice, the pain compounds across departments. Inconsistent inputs from business units, no staleness detection on evidence records, missed deadlines surfaced only when someone manually checks a tracker – these are not edge cases. They are the standard operating condition for organizations that treat compliance evidence as a byproduct of annual reviews rather than daily work.
Why This Matters Now
Three forces have made the gap between "we do compliance" and "we operate compliantly" untenable.
Filing deadlines are procedural, not advisory. Once authorities request clarification, completion, or correction, organizations can quickly lose control of the timetable if evidence and ownership are scattered. Teams that assemble dossiers under pressure often miss practical filing windows, not because they lack the substance, but because they lack the operational infrastructure to produce it on time.
Multi-framework obligations overlap. A single business process can generate compliance obligations under multiple regulatory frameworks simultaneously. Each framework expects its own evidence, its own filing format, its own timeline. Manual processes that barely manage one framework collapse under the weight of three or four running concurrently. The organizations that invested in policy but stopped short of operational infrastructure are the most exposed.
Auditors expect contributor lineage, not just outputs. It is no longer sufficient to produce a completed form. Regulators and internal auditors increasingly expect to see the chain: who contributed a specific section, who reviewed it, who approved it, when each step occurred, and whether the current version reflects the latest organizational state. A signed PDF does not answer these questions. A structured audit trail does.
What Structured Operational Compliance Looks Like
Operational compliance maturity is not a binary state. It is a set of capabilities that, taken together, transform compliance from a periodic documentation exercise into a continuous operational function. Five markers distinguish organizations that have made this shift.
1. Evidence Is a Byproduct of Work
In a mature compliance operation, completing a task produces the evidence record automatically. When a department contributor fills out their section of a DPIA, the system captures who submitted it, when, and what changed from the previous version. Evidence is not assembled after the fact, it accumulates as work happens.
2. Contributor Lineage Is Structural, Not Reconstructed
Every compliance deliverable traces through a defined chain: contributor, reviewer, approver, submitter. This is not a matter of adding names to a cover sheet. It means each role in the chain is assigned before work begins, each handoff is recorded, and the complete lineage is available for any record at any time. When an auditor asks who prepared the risk assessment section of a filing, the answer is immediate and verifiable.
3. Deadlines Drive Workflow, Not Just Notifications
Operational compliance connects regulatory deadlines to specific tasks, assigns responsibility for each stage, and escalates when milestones approach or are missed. A deadline is not a calendar reminder, it is a workflow trigger with dependencies, escalation rules, and clear ownership. When a department misses a contribution deadline, the system surfaces the gap before it becomes a missed filing window.
4. Multi-Department Coordination Has a Single Source of Truth
Compliance work crosses department boundaries by definition. A DPIA dossier may require inputs from legal, IT security, HR, marketing, and procurement. Operational maturity means these inputs converge in a single structured record, not in email threads or parallel spreadsheets. Each department sees its obligations, the current state of its contributions, and the status of the overall filing.
5. Submission-Readiness Is the Default State
When a regulator or auditor requests a dossier, an operationally mature organization does not begin assembly. The dossier already exists as a structured, version-controlled record with complete contributor lineage. Evidence packs are assembled from existing approved records, not recreated under pressure. The attestation cycle follows a defined lifecycle, draft, review, approval, submission, with each stage tracked.
How ComplianceOne Supports This
AesirX ComplianceOne is designed around the principle that compliance evidence should emerge from structured work, not from separate documentation projects.
Task & workflow management decomposes compliance obligations into assigned tasks with deadlines, dependencies, and escalation rules. Each regulatory filing becomes a structured workflow, not a project plan in a general-purpose tool. Tasks carry ownership, due dates, and dependency chains. When a predecessor task is late, downstream owners are notified before their own deadlines are affected.
Audit trail captures every action – field edits, review approvals, submissions, status changes – with a 4-role contributor chain: contributor, reviewer, approver, and submitter. This is the structural lineage layer that transforms "we completed the filing" into "here is exactly who did what, when, and with what approval." The audit trail is not a log bolted onto the side of the system. It is the evidentiary foundation that every other module writes to.
Compliance forms provide structured templates aligned to regulatory requirements. Forms enforce completeness, required fields, section-level review gates, and version tracking. When a form moves through its lifecycle, the evidence record builds automatically. The output is a submission-ready package, not a document that needs manual formatting before filing.
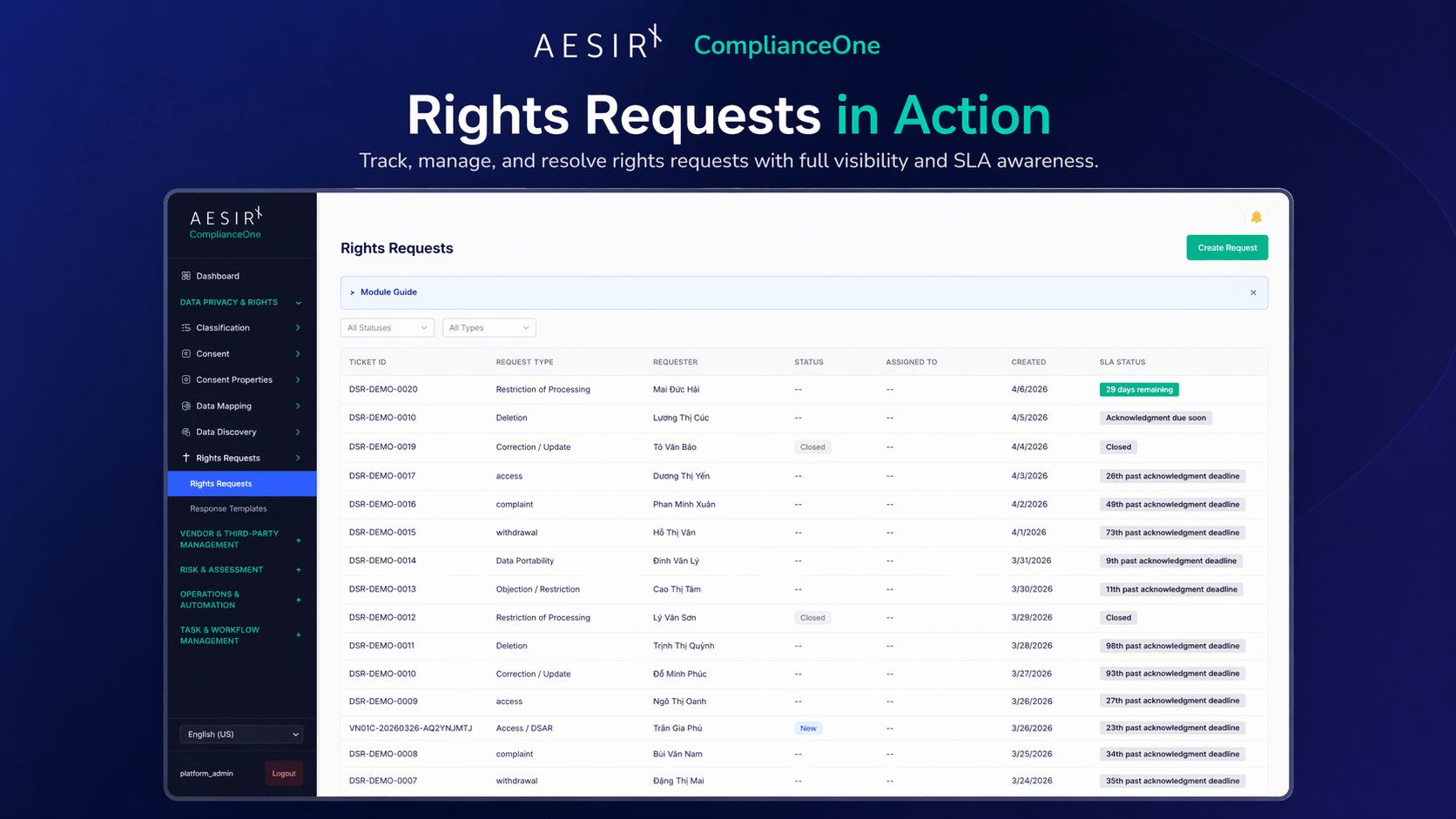
Data privacy & rights management handles the operational side of data subject interactions – receiving requests, routing them to responsible teams, tracking response timelines, and maintaining the evidence trail that demonstrates systematic handling rather than ad hoc responses.
Role-based access ensures that contributor assignments match organizational authority, so contributors, reviewers, approvers, and submitters can only act within the responsibilities assigned to them. The RBAC model is not a simple admin/user split. It maps to the compliance reality where different roles have different authorities – a department contributor can submit inputs, a compliance officer can review them, a DPO can approve them, and a designated submitter can file them with regulators.
Key Takeaways
- Operational compliance means evidence accumulates during work, not after it. If your team assembles compliance documentation as a separate project before each audit or filing, you have a documentation operation, not a compliance operation.
- Contributor lineage is the foundation of audit readiness. Knowing who contributed what, who reviewed it, when each step occurred, and whether the current version is approved – this is what separates defensible compliance from hopeful compliance.
- Deadlines must drive workflows, not just reminders. Regulatory windows (30-day reviews, 15-day supplements, 10-day resubmissions) are procedural. Missing them has operational consequences. Deadline management must be embedded in task workflows with escalation paths.
- Multi-department coordination requires a single structured record. When five departments contribute to a single filing, parallel spreadsheets and email threads produce version conflicts and accountability gaps. One record, one lineage chain, one source of truth.
- Submission-readiness should be the default, not a sprint. An annual attestation pack generated from current approved records is a five-minute export. An attestation pack assembled from departmental cut-and-paste is a two-week project with no assurance of accuracy.
Next Steps
Start a 30-day pilot. Deploy ComplianceOne against your most pressing compliance workflow – a DPIA dossier, an annual attestation cycle, or a multi-framework filing obligation. Measure the difference between your current evidence assembly process and a structured operational model. The pilot includes module configuration, workflow setup, and a maturity baseline assessment.
Schedule a compliance operations consultation. Walk through your current operational state with a compliance specialist. The consultation maps your existing evidence flows, identifies the gaps between documentation and operational readiness, and defines a structured path to compliance maturity – prioritized by regulatory risk and filing deadlines.