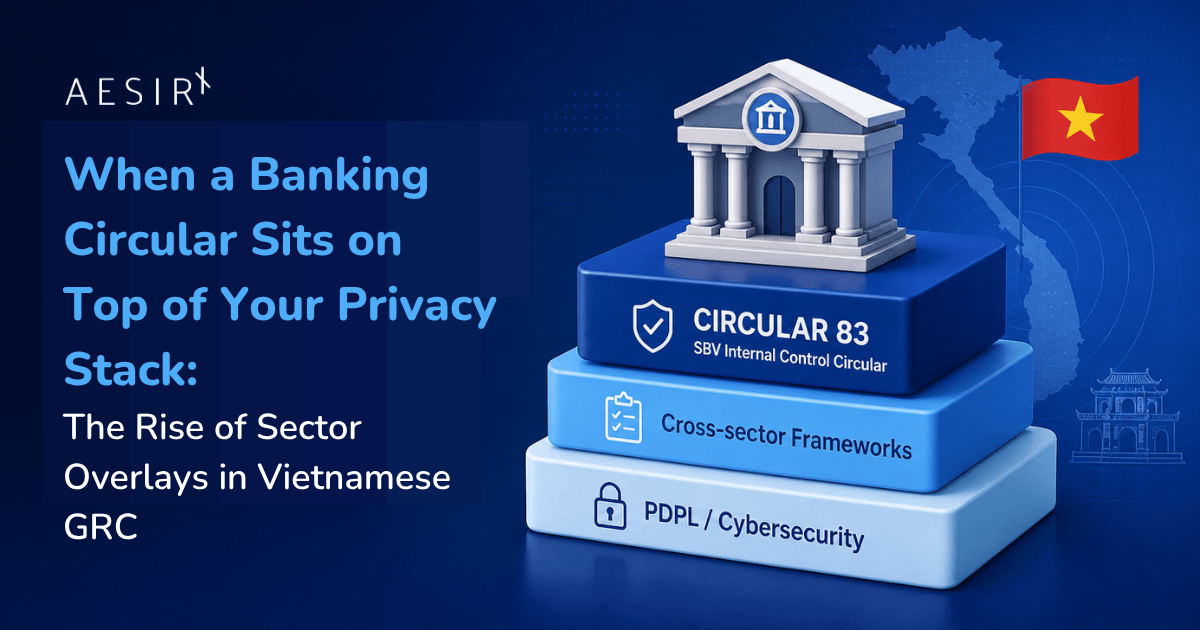
TL;DR: Most GRC platforms treat regulation as horizontal. You install one framework for personal data protection, another for cybersecurity, another for cross-border transfers, and you assume the same controls satisfy every industry. Banks, payment intermediaries, insurers, telcos, and healthcare operators discover the limit of that model the first time a sector regulator asks for evidence the horizontal frameworks were never designed to produce. Vietnam's State Bank has just made that limit explicit. Thông tư số 83/2025/TT-NHNN, the new internal control circular for commercial banks and foreign bank branches, is not a data protection law. It does not reuse PDPL articles. It does not impose monetary fines. It is a sectoral governance instrument, and it sits on top of the data protection and cybersecurity stack a bank already runs. AesirX ComplianceOne now ships the first sector overlay in the platform: a Circular 83 pack that captures the four annual SBV reporting templates, the supporting internal control records, the supervisory risk model, and the phased deadline engine that wires the 2028 obligations into operational workflow. This article explains what a sector overlay actually is, why it is structurally different from cross-sector frameworks like PDPL or GDPR, and what changes when regulatory layering becomes a first-class concept in your compliance platform.
This article is written for CISOs, heads of compliance, internal audit leads, risk officers, and legal counsel in Vietnamese banks, foreign bank branches, payment intermediaries, and the multi-sector groups (bancassurance, banking plus telecom, banking plus e-commerce) that already operate under PDPL, Decree 356, the Cybersecurity Law, and the broader regulatory stack. It is also relevant to insurance, healthcare, telecom, payments, and energy operators who will face their own sector overlays in the coming years.
The control review that two compliance officers ran in parallel
A commercial bank in Ho Chi Minh City finishes its annual personal data protection self-assessment in the middle of the year. The DPO files the dossier with the Ministry of Public Security, archives the supporting evidence, and closes the work. The platform records the contributors, the approvals, the timestamps, and the version that was filed.
Two months later the head of internal audit pulls a different file. The State Bank wants the bank's annual control activity self-assessment. It wants the annual risk management report. It wants the annual internal capital adequacy assessment report. It wants the annual internal audit report. It wants them on official SBV templates, on a calendar driven by the bank's fiscal year, signed off by named functions inside the bank, and filed within ninety days of period end. Sixty days for the internal audit report. Seven working days when an ad hoc audit lands.
The DPO's dossier does not satisfy any of these. The personal data assessment was the right work for the wrong regulator. The bank now has to assemble a parallel evidence pack, on different templates, against a different supervisory expectation, with a different review function inside the bank acting as the lead. None of the underlying work is wasted. The risk register, the control catalogue, the third party records, the incident log, the policy review history are all reusable. But the framing is sectoral, not horizontal, and the platform that holds the evidence has to know the difference.
“Horizontal frameworks tell you what every organisation must protect. Sector overlays tell you what your industry's regulator will ask for.”
That is the structural shift Circular 83 forces. And it is the shift that turns a generic GRC platform into something a bank can actually operate.
Why Circular 83 is not a data protection law
The full Vietnamese title is Thông tư số 83/2025/TT-NHNN quy định về hệ thống kiểm soát nội bộ của ngân hàng thương mại, chi nhánh ngân hàng nước ngoài. Issued by the State Bank of Vietnam, it regulates the internal control system of commercial banks and foreign bank branches. Its main effective date is 1 July 2026. A second tranche of obligations, covering stress testing, risk data management, model risk, and interest rate risk in the banking book, becomes effective on 1 January 2028. Banks that wish to implement those obligations early must notify the State Bank within ten calendar days of doing so.
Circular 83 spans five intake layers and seventeen layer themes. Sector applicability defines exactly which entities the instrument binds. Governance and internal control covers three lines of defence, board oversight, the compliance, risk, and audit functions, delegated authority, and ethics. Risk management covers material risk taxonomy, appetite, limits, stress testing, internal capital adequacy assessment, and new product review. Management information and reporting covers the integrity, timeliness, and security of the information that flows up to the board and out to the regulator. The fifth layer is the SBV reporting cadence itself: the official templates, the ninety, sixty, and seven working day windows, and the supporting appendices for technical references like IRRBB and capital indicators.
The instrument's character is the part that surprises most readers. There are no monetary fines in Circular 83. There is no schedule of administrative penalties. The enforcement mechanism is supervisory: ten supervisory risk areas, each with severity tiers from low to critical, against which the State Bank's inspection function maps observed weaknesses to escalating supervisory consequences. Late or missing reports. Governance evidence gaps. Weak or undocumented controls. Missing risk appetite or limits. Internal audit independence failures. Outsourcing due diligence gaps. Failure to remediate known weaknesses. Performance without provability. The currency of compliance under Circular 83 is supervisory standing, not fine avoidance, and the unit of evidence is documented, signed, and dated control activity, not the absence of an incident.
This is structurally distinct from PDPL and Decree 356, which sit alongside Circular 83, not inside it. A bank in Vietnam is bound by both. The data protection officer continues to file personal data dossiers and breach notifications under the data protection regime. The internal audit, risk, and compliance functions now file the four annual SBV reports under the internal control regime. The two streams share evidence, but the regulators, the templates, the deadlines, the supervisory consequences, and the lead functions inside the bank are different.
What a sector overlay actually is
A sector overlay is a regulatory pack that applies only to organisations operating in a specific industry, layered on top of the cross-sector frameworks every organisation already runs. PDPL, the Cybersecurity Law, ISO 27001, and SOC 2 are horizontal: a software vendor, a hospital, and a bank can all install them and the obligations apply broadly the same. A sector overlay is vertical: it binds only the entities the sectoral regulator defines, on terms specific to that industry's supervisory model.
In ComplianceOne the overlay carries three distinguishing properties. It declares its direct scope as a list of entity types: commercial banks and foreign bank branches in Circular 83's case. It declares itself as optional at the platform level, because not every tenant is a bank. And it declares its sector against an eleven value taxonomy that covers banking, insurance, healthcare, ICT critical infrastructure, telecom, energy, transport, digital services, public administration, payments, and a residual category for sectors the platform has not yet modelled.
When a tenant installs the overlay, the platform does not assume the bank's view. It asks. If the organisation has self identified as banking in its sector profile, the overlay installs in direct mode: deadlines schedule, dashboard widgets surface, the framework contributes to the compliance score, and the framework detail page displays a green banner reading "directly applicable to your organisation." If the organisation has not self identified as banking, the overlay still installs (because content authors, consultants, and multi sector groups still benefit from the reference material), but in reference mode: deadlines suppress, dashboard widgets hide, the framework does not contribute to the compliance score, and the banner reads in amber, "reference only, your organisation is not classified as banking." The mode is editable at any time through the framework detail page, and every mode change is captured in the audit trail with the actor, the timestamp, and the previous and new values.
The opt in and the mode switch are the operational consequence of the structural distinction. Cross sector frameworks default on. Sector overlays default off, and they default scoped, because the cost of a non banking tenant being silently held to banking deadlines is a worse outcome than the cost of a banking tenant having to flip a setting once.
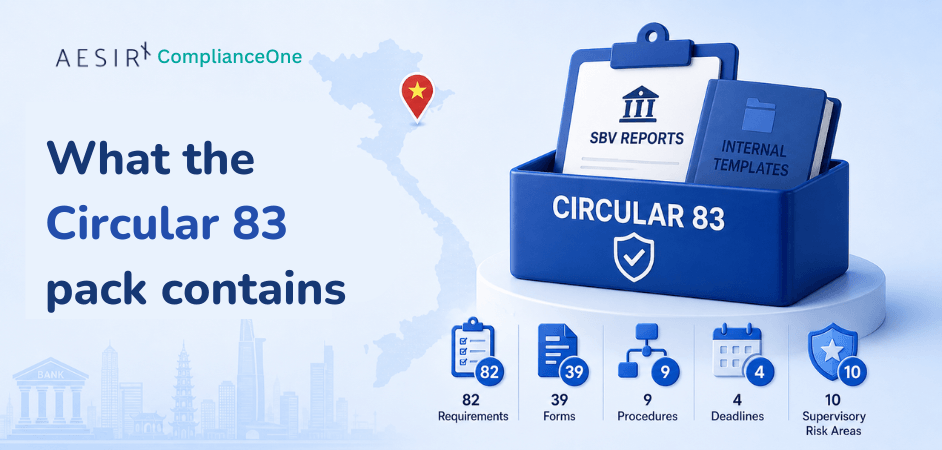
What the Circular 83 pack actually contains
The pack ships eighty two requirements distributed across the seventeen layer themes. It ships thirty nine forms in two groups: the official SBV reporting templates and technical reference appendices on one side, and the internal operational templates that produce the evidence those reports rely on, on the other. The four annual SBV reports cover control activity self assessment, risk management, internal capital adequacy assessment, and internal audit, each on a regulator defined template. Two technical references cover interest rate risk in the banking book and capital indicators, with evidence attachment slots rather than submission requirements. The remaining thirty three internal templates cover the underlying control work: scope records, three lines of defence matrices, control activity registers, senior management supervision, compliance reviews, policy governance, conflict of interest controls, delegated authority, risk appetite statements, material risk registers, risk limit registers, risk data governance checklists, new product and market reviews, stress testing evidence placeholders, internal capital adequacy assessment evidence packages, model risk evidence placeholders, management information system reviews, internal reporting registers, SBV submission tracking, supervisory findings and remediation logs, internal audit plans and findings and corrective actions, outsourcing registers, third party due diligence, outsourcing contract checklists, outsourcing business continuity evidence, and the early implementation notification record.
The pack ships nine procedures that name the workflows the bank actually runs: the four annual reports, the ad hoc internal audit report, policy and internal rule review, outsourcing and third party risk review, the management information system review, and the early implementation notification. Each procedure declares its trigger, its steps, the responsible function, the outputs it produces, the related forms it consumes, and the SBV submission channel when one applies.
The pack ships four deadlines in the cadence the State Bank actually uses: ninety days for the three financial year annual reports, sixty days for the annual internal audit report, seven working days for ad hoc internal audit reports, and ten calendar days for the early implementation notice window. The deadlines do not float in the abstract. They activate against the framework's effective date, the bank's fiscal year, and the bank's actual implementation choices, including the early implementation flow for the 2028 obligations.
The pack ships ten supervisory risk areas with severity tiers, ordered from critical to low, covering reporting, governance, internal control, risk management, internal audit, policy governance, management information and data governance, outsourcing, remediation, and the residual category for requirements performed but unprovable. The supervisory risk model is what replaces a fine schedule under Circular 83. It is also what an internal audit function uses to triage its own findings against the lens the State Bank itself will apply.
The pack ships authoritatively in English and Vietnamese. The remaining locales currently carry English adjacent placeholders; the full multilingual pass is on the roadmap and is not claimed in this article.
Phased obligations and the regulatory deadline engine
Most regulators do not move all of their obligations on a single day. Circular 83's stress testing, risk data, model risk, and IRRBB measurement obligations land on 1 January 2028, two and a half years after the main effective date. A bank that wants to implement those obligations early must notify the State Bank within ten calendar days. That is not a calendar setting. It is a workflow.
ComplianceOne now treats phased obligations as a first class concept across regulatory packs. A pack can declare that a specific deadline is triggered by a phased obligation, and the platform's deadline engine resolves the activation date as the later of the framework's main effective date and the phased obligation's effective date. When a bank elects early implementation, the platform records the election against the obligation, the audit trail captures who made it and when, and the ten day notification deadline activates from the elected effective date. The notification record itself is a form in the pack, with the bank as preparer and the State Bank as recipient, on a tracked channel.
The mechanism is not banking specific. Other Vietnamese instruments and other sector overlays will use the same engine for their own phased timelines. Circular 83 is the first concrete consumer because it has the most operationally complex phased schedule on the platform today. The architecture was generalised at the same time the overlay was authored, on purpose: regulatory layering needs regulatory time as a primitive, not as a workaround.
The annual SBV reporting cycle, walked end to end
The head of internal audit at a commercial bank opens the deadlines surface in mid January. The bank's fiscal year closed on 31 December. Three annual reports are now sixty to ninety days from filing, and one is sixty days. The control activity self assessment is owned by the compliance function. The risk management report is owned by the risk function. The internal capital adequacy assessment report is owned by the risk function in coordination with finance. The internal audit report is owned by internal audit. Each of the four reports has an official SBV template, a named preparer inside the bank, an approval chain that ends with the board level committee responsible for that domain, and a submission channel into the State Bank's supervisory unit.
The compliance manager opens the control activity self assessment workflow. The procedure declares the trigger (financial year end), the steps (compile control activity register, run control self assessment, document deficiencies, propose remediation, route to compliance committee, route to board), the responsible function at each step, and the supporting forms. The control activity register is already populated from the year's daily control work: every control test, every policy review, every conflict of interest declaration, every delegated authority change, every senior management supervision record. The self assessment is not assembled from scratch. It is composed from the operational evidence the bank already produced.
The risk officer follows the same pattern on the risk management report. The risk appetite statement, the material risk register, the risk limit register, the new product and market review records, and the stress testing evidence placeholders all feed into the report. The internal capital adequacy assessment report draws on the same risk inventory plus the capital indicators reference appendix and the bank's own internal capital methodology.
The internal audit lead works on a sixty day window, not ninety. The audit plan, the engagement findings, the corrective action register, the supervisory findings and remediation log, and the independence evidence assemble into the annual internal audit report. If a serious matter arose during the year that triggered an ad hoc engagement, the seven working day window applies to that engagement separately, and the platform tracks it against its own deadline.
Every step generates evidence that is timestamped, contributor attributed, version controlled, and linked back to the requirement it satisfies. When the State Bank's inspection function arrives, the bank is not assembling a dossier. It is exporting a snapshot.
The early implementation election, walked end to end
A foreign bank branch with a strong existing risk data infrastructure decides in early 2026 that it will implement the 2028 phased obligations in mid 2027. The risk officer opens the framework detail page, navigates to the phased obligations panel, and selects the obligation. The panel reveals the early implementation flow. The officer enters the chosen effective date. The platform validates that the chosen date is not before the framework's main effective date and that a notice window is configured. The election is recorded. The audit trail captures the actor and the timestamp.
The notification deadline activates immediately. A form opens for the SBV early implementation notice. The risk officer prepares it with the chosen obligations, the chosen effective date, and the rationale. The form routes through the bank's review chain, ends at the senior officer who signs off on State Bank correspondence, and submits through the recorded channel. The submission is logged against the deadline. The deadline closes. The phased obligation is now active for that bank from the elected date forward, and the four annual reports for the bank's next fiscal year include the previously dormant requirements.
None of this is a one off engineering effort. The same flow will run for every future phased obligation in every future sector overlay. The bank's compliance function does not need to remember the ten day window. The platform does.
The shift: from horizontal compliance to layered compliance
The mental model that sustained the first generation of GRC platforms was a horizontal one. Pick the frameworks that apply, install them side by side, run controls that satisfy as many at once as possible, file the dossiers when the deadlines come. That model still works for the cross sector layer. It does not survive contact with sectoral supervision.
Sectoral regulators do not write to the same template the data protection regulator writes to. They do not share the data protection regulator's deadlines, supervisory consequences, or evidence taxonomy. They expect the regulated entity to know the difference, to staff the difference, and to file on the difference. A platform that flattens that distinction puts the bank's compliance officer in the position of doing the layering manually, in a spreadsheet, every quarter, forever.
The shift is to treat regulatory layering as a primitive of the platform, not as a project the customer runs. That means a sector taxonomy the tenant declares once and the platform respects everywhere. It means installation modes that distinguish "this binds you" from "this is reference material." It means deadline engines that treat phased obligations as scheduled events with their own notice windows. And it means evidence flows that compose, not compete: the personal data work the DPO does and the internal control work the compliance function does feed each other where they overlap, and stay distinct where they should.
Circular 83 is the first sector overlay in ComplianceOne. It will not be the last. The same pattern is queued for insurance, healthcare, telecom, payments, and energy. The architecture exists now because the bank that needs it could not wait for the second.
Closing
The bank that satisfies its data protection obligations and assumes the State Bank will be satisfied is a bank that has not yet read Circular 83. The internal control system the State Bank now requires is not a subset of personal data protection, and it is not a relabelled copy of ISO 27001 or SOC 2. It is sectoral governance, with sectoral templates, on a sectoral cadence, judged on sectoral supervisory criteria. A GRC platform that respects that structure makes the bank's job tractable. A GRC platform that flattens it makes the bank's job theatrical.
If you want to see how a sector overlay actually behaves in a working compliance platform, with the install modes, the supervisory risk model, the four annual SBV reports, and the phased deadline engine wired together, you can explore the live capability at https://aesirx.io/compliance-one. We would also be happy to walk you through the Circular 83 pack against your bank's actual reporting calendar.
Ronni K. Gothard Christiansen
Technical Privacy Engineer & CEO, AesirX.io
Laws and instruments referenced
- Thông tư số 83/2025/TT-NHNN: internal control system of commercial banks and foreign bank branches (State Bank of Vietnam)
- Luật Bảo vệ dữ liệu cá nhân (PDPL): Vietnam Personal Data Protection Law
- Nghị định 356/2025/NĐ-CP: implementing decree for personal data protection
- ISO/IEC 27001:2022: Information security management systems
- AICPA Trust Services Criteria (SOC 2)
Disclaimer: This article is for informational purposes only and does not constitute legal advice. Banks and foreign bank branches should consult qualified Vietnamese legal counsel and the State Bank of Vietnam's official guidance for binding interpretation of Circular 83.