TL;DR: Compliance is not a documentation project. It is an operational system. The difference between an organization that "has policies" and one that can actually prove compliance under pressure comes down to evidence – and evidence must be generated as a byproduct of daily work, not reconstructed when a regulator asks. A GRC platform is the systematic layer that makes this possible: every form completed, every task assigned, every data mapping approved, every review signed off, every assessment submitted becomes part of the evidence trail. This article explains why that shift matters, how it works in practice, and what it looks like across real compliance workflows.
This article is written for DPOs, compliance managers, CISOs, legal counsel, audit leads, and governance teams, especially those operating in regulated industries where "we're compliant" must be demonstrable, not declarative.
The moment compliance becomes real
Your audit lead receives a regulatory inquiry. The scope: personal data processing across three departments, vendor governance controls, and cross-border transfer documentation. They need to produce an evidence pack showing who completed each compliance step, when it was reviewed, who approved it, and whether submissions happened before regulatory deadlines.
The clock is ticking.
In that moment, only one thing matters: can your organization produce the evidence? Not the policy. Not the slide deck. Not the compliance roadmap from last year's board presentation. The actual evidence – structured, traceable, and audit-ready.
“The compliance question regulators ask is never 'do you have a policy?' It is 'can you show me the evidence trail?”
Most organizations discover too late that they cannot. Not because they failed to do the work, but because the work was never captured in a way that produces evidence. That gap – between doing compliance and proving compliance – is what a GRC platform is designed to close.
Why policy-only compliance fails
Every compliance program starts with policies. Data protection policies. Vendor management policies. Incident response plans. Access control frameworks. These are necessary. They are also radically insufficient.
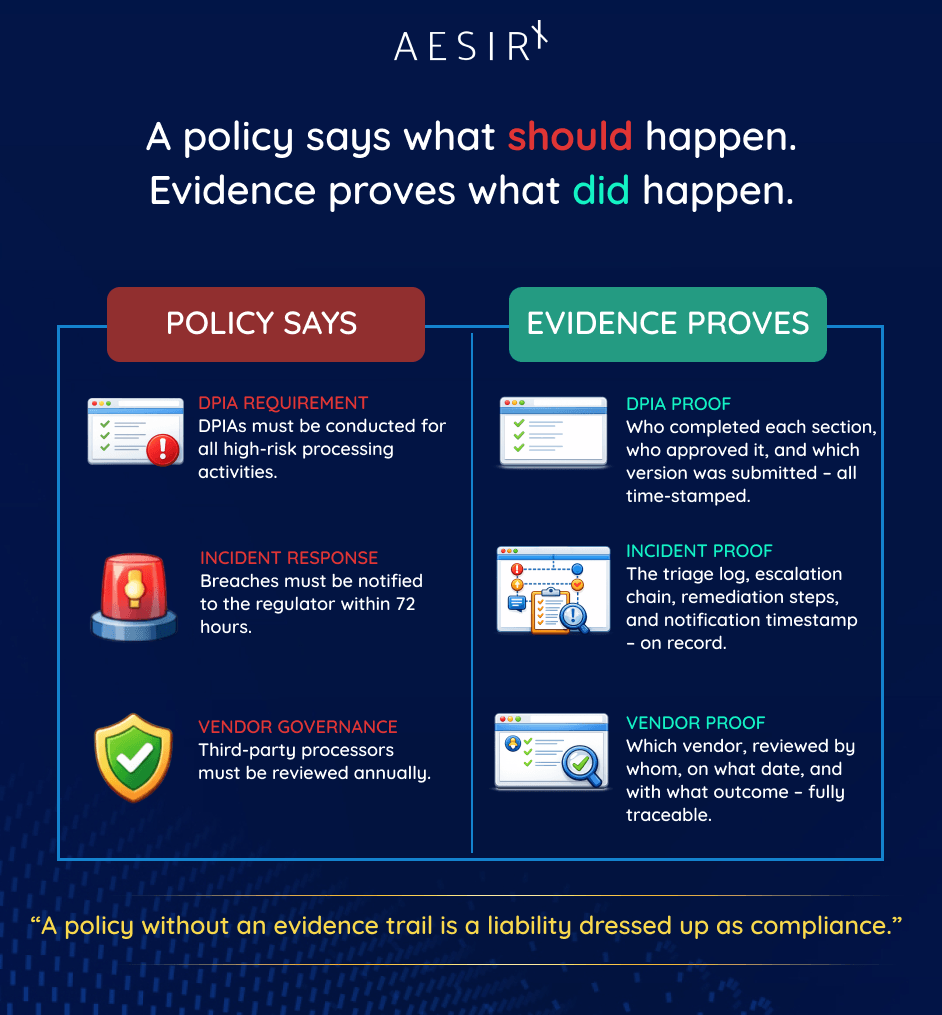
A policy says what should happen. It does not prove what did happen.
Consider what happens when compliance lives in policy documents alone:
- A data protection policy states that DPIAs must be conducted for high-risk processing. But when the regulator asks for the DPIA, the organization must reconstruct it from email threads, shared drives, and individual recollections of meetings that happened months ago.
- An incident response plan outlines a 72-hour notification window. But when the breach occurs, there is no structured workflow to capture the triage, the escalation, the remediation steps, or the notification timeline in a way that produces a defensible record.
- A vendor management policy requires annual reviews of third-party data processors. But the evidence of those reviews lives in scattered spreadsheet tabs, and nobody can show which vendor was reviewed by whom, when, or what the outcome was.
“A policy without an evidence trail is a liability dressed up as compliance.”
The failure mode is not ignorance. The teams did their jobs. The DPO reviewed the processing activity. The incident response team triaged the breach. The procurement lead checked the vendor. But none of it was captured in a system that produces traceable, structured, time-stamped evidence.
When the regulator asks, the answer is silence – or worse, a frantic reconstruction effort that looks exactly like what it is: an organization trying to prove after the fact what it should have been documenting all along.
Why ad hoc compliance breaks down in practice
Some organizations move past policy-only compliance into what looks like operational compliance, but built on ad hoc tools. Shared spreadsheets for tracking DPIAs. Email chains for vendor reviews. A project management tool repurposed for incident tracking. A shared drive for "evidence."
This approach works until it does not. And it stops working at exactly the worst moment: when someone external needs to verify it.
Ad hoc compliance breaks down because:
Evidence is fragmented across tools.
A single DPIA filing might involve inputs in a spreadsheet, approvals in email, a form in a PDF, and a submission record in someone's personal notes. Assembling this into a coherent evidence pack takes days.
There is no contributor lineage.
When 15 departments contribute to a filing – retail banking, HR, marketing, IT security, procurement – who provided what content, and when? In a spreadsheet, that history does not exist.
Version control is manual.
Which version of the cross-border transfer assessment was submitted? The one in the shared drive, the one attached to the email, or the one on the DPO's laptop? Nobody is certain.
Approval chains are invisible.
The DPO approved the filing. Can you prove it? With a timestamp? With the version they actually reviewed? With the specific changes they approved?
Deadlines are tracked in calendars, not in systems.
A 30-day filing review period, a 15-working-day supplement window, a 10-working-day resubmission deadline; these statutory timelines get lost in personal task lists and email reminders.
“The problem with ad hoc compliance is not that people are careless. It is that the tools they use do not produce evidence as a byproduct of the work.”
The audit lead who must assemble a cross-framework evidence pack across seven regulatory frameworks does not have a completeness dashboard. They have a mental model of where things probably are, a series of requests to colleagues, and a deadline they cannot extend.
Why evidence must be generated operationally, not reconstructed later
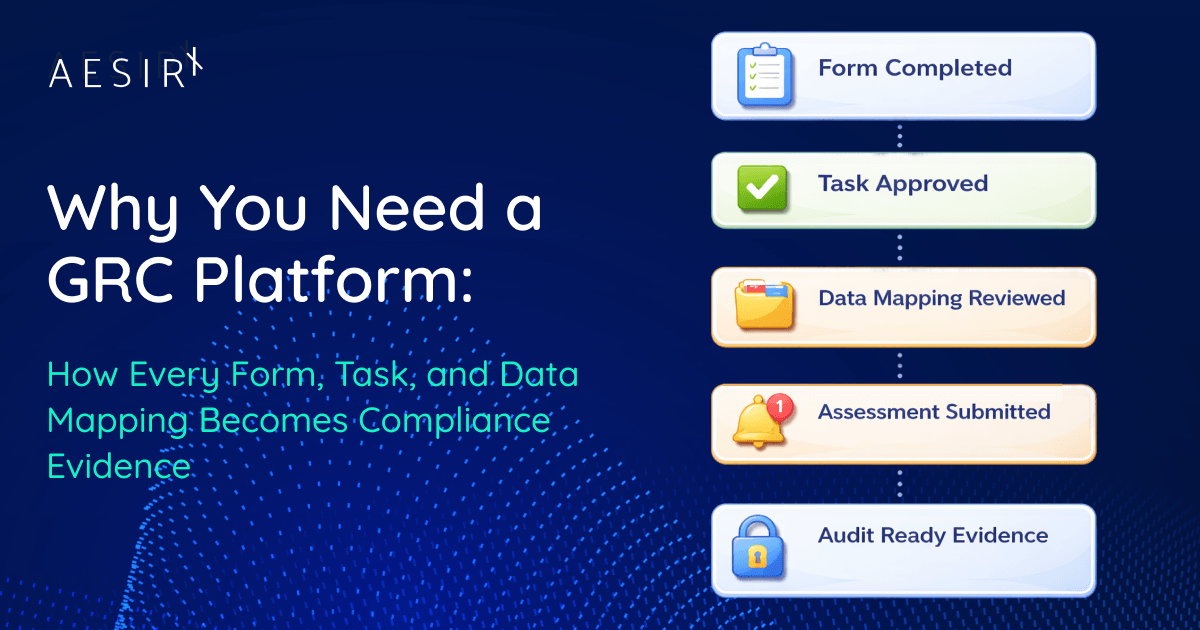
The fundamental insight behind a GRC platform is simple: evidence should be a byproduct of doing the work, not a separate project conducted after the work is done.
When a department data owner completes their section of a DPIA filing, that completion is evidence. The system records who completed it, when, what fields they filled, and which version they worked on. No separate documentation step is required. The act of doing the work is the act of creating the evidence.
This principle applies across every compliance operation:
A form completed is evidence generated. When a compliance officer fills out an official filing form – say a DPIA annex or a data governance attestation – the structured data captured, the contributor identity, and the timestamp together constitute the evidence. The form itself is the proof.
A task assigned and completed is evidence generated. When the DPO assigns a section to the HR department and the department data owner completes it, that task lifecycle – assignment, acceptance, completion, review – is the evidence of multi-department participation in the filing.
A data mapping reviewed is evidence generated. When a data governance lead reviews and approves a processing activity inventory, with cross-border transfer flags and sensitivity classifications, that review action becomes part of the evidence chain for any subsequent audit.
An assessment submitted is evidence generated. When a DPIA dossier moves from draft to internal review to approved to submitted, each state transition is a documented milestone with a responsible party and a timestamp.
A control verified is evidence generated. When a vendor risk assessment is completed and a formal risk acceptance is recorded, that acceptance – with the reviewer identity, the date, and the specific findings – is audit-ready evidence of vendor governance.
A review signed off is evidence generated. When the DPO reviews and approves a consolidated filing before submission, that approval – recorded with the exact version reviewed and the approval conditions – proves the governance chain.
An audit action completed is evidence generated. When an audit lead opens an inspection case, selects the frameworks in scope, and assembles an evidence pack, the case itself (with its completeness dashboard, gap log, and sign-off chain) becomes the audit evidence.
“In a well-designed GRC platform, you never create evidence. You generate it by doing the work.”

This is not a philosophical point. It is an operational architecture decision. The system must be designed so that every meaningful compliance action – every form entry, every task completion, every approval, every review, every submission – automatically produces a structured, time-stamped, attributable record that can be retrieved, exported, and presented under regulatory scrutiny.
How personas, use cases, and workflows connect to this reality
A GRC platform is not a generic form builder. It is a system designed around the actual workflows that real compliance roles execute every day. The evidence framework works because the platform understands who does what, why, and in what sequence.
The Enterprise DPO filing a DPIA dossier
Consider the Group DPO at a large financial institution – responsible for PDPL compliance, Decree 356 implementation, breach handling, data subject requests, and DPIA filings with the Ministry of Public Security.
Today, without a platform, this DPO faces:
- Inconsistent department inputs – each department formats responses differently, uses different tools, delivers at different times.
- No single source of truth – filings are assembled from email threads, spreadsheets, and shared drives with no version control.
- Accountability gaps – hard to prove who supplied what content and when, especially under authority scrutiny.
- Missed deadlines – filing review periods, supplement loops, and resubmission windows get lost in email.
In a GRC platform, the DPIA workflow becomes an evidence-generating operation:
- The DPO creates a DPIA case and selects the correct official form (Phụ lục I for standard processing, Phụ lục II for cross-border or high-risk).
- Sections are assigned to department data owners across retail banking, HR, marketing, IT security, and procurement.
- Each department completes their section within the platform – every field entry is attributed and time-stamped.
- The platform consolidates departmental inputs into a master dossier, flagging conflicts and missing sections.
- The DPO reviews the consolidated filing, returns sections for correction where needed, and approves the final dossier.
- Submission is logged with channel selection (MPS portal, in-person, postal) and the filing enters lifecycle tracking.
- Supplement requests and resubmissions are linked to the original dossier with full lineage.
Every step in this workflow – every department contribution, every review comment, every approval action, every submission milestone – is captured as structured evidence. When a regulator asks "show me the DPIA," the answer is not a PDF. It is a complete evidence chain showing how the dossier was built, who contributed what, who reviewed it, who approved it, when it was submitted, and what happened after.
The Audit Lead assembling a cross-framework evidence pack
Now consider the Internal Audit and Regulatory Inspection Lead – responsible for evidence collection, completeness assessment, and export across multiple regulatory frameworks simultaneously.
Today, without a platform, this role faces:
- Framework silos – evidence for PDPL, Data Law, E-Commerce, Telecom, Cybersecurity, and AI frameworks lives in separate systems with no unified view.
- No completeness dashboard – impossible to see at a glance what evidence exists, what is missing, and what has gaps.
- Lost approval history – approval chains for individual filings are not attached to the evidence when pulled into an audit pack.
- Manual pack assembly – combining evidence from multiple frameworks into one coherent export is a multi-day manual process.
In a GRC platform, the audit workflow becomes systematic:
- The audit lead opens an inspection case and selects the frameworks in scope
- The platform automatically pulls relevant cases, templates, and evidence for each framework.
- A completeness dashboard shows evidence status by framework, case, template, and evidence type.
- Tasks are assigned to department owners and framework owners for missing evidence or exception resolution.
- Every artifact is traceable back to its original case with full approval and submission history.
- Gaps and exceptions are flagged visibly, never hidden in email threads.
- The consolidated audit pack is routed through framework owner review, legal review, and internal audit sign-off.
- The final export includes all appendices: evidence, gaps, approval history, submission history, and linked cases.
The evidence pack is not assembled from scattered sources. It is extracted from the same system where the compliance work was done. The evidence already exists because the platform generated it as a byproduct of every form, task, assessment, review, and approval that was completed throughout the year.
The Data Governance Lead running annual attestation
The Data Governance Lead responsible for the organization's data inventory, classification, and governance controls faces a parallel challenge. Annual governance attestation requires proof that data inventories are current, classifications are reviewed, retention schedules are enforced, and governance controls are operating.
In a GRC platform, every data mapping review, every classification decision, every retention policy acknowledgment, and every governance control verification is captured as evidence. The annual attestation does not require a reconstruction project – it requires an export of the evidence that was generated operationally throughout the year.

Why a GRC platform becomes the systematic layer
The pattern across all of these workflows is the same: compliance evidence must be generated as a structural byproduct of operational work, not as a separate documentation project.
A GRC platform provides this systematic layer by enforcing five architectural principles:
Structured data capture at the point of work. Every form, every field, every selection is captured as structured data, not as a free-text document that must be parsed later. When a department data owner completes their DPIA section, the data enters the system in a structured format that can be queried, exported, and verified.
Contributor lineage on every action. Every action in the system is attributed to a specific user with a timestamp. Who filled this field? Who reviewed this section? Who approved this filing? Who submitted it? The platform answers these questions automatically because it records them as the work happens.
Workflow state as evidence. The lifecycle of every case – draft, in review, returned for correction, approved, submitted, supplemented, resubmitted, closed – is itself evidence. State transitions are documented milestones that prove governance was followed.
Cross-module traceability. A DPIA filing connects to data mappings. A vendor review connects to risk assessments. An incident response connects to breach notification filings. A GRC platform maintains these connections so that evidence can be traced across compliance domains, not just within them.
Export-ready evidence packs. When the audit lead needs an evidence pack, the platform can produce it – with framework-by-framework sections, completeness indicators, gap logs, approval chains, and full case lineage – because the evidence was structured from the moment it was created.
“A GRC platform does not create compliance. It makes compliance demonstrable – by turning every operational action into part of the evidence trail.”
The shift: from compliance as a project to compliance as an operating system
The organizations that struggle most with regulatory scrutiny are not the ones that ignore compliance. They are the ones that treat compliance as a periodic project – a DPIA conducted once, a vendor review done annually, an audit preparation sprint triggered by an upcoming inspection.
The shift is to treat compliance as an operating system. Not something you do periodically, but something the organization runs continuously. Every department data owner who completes a task is generating evidence. Every DPO who reviews a filing is generating evidence. Every governance lead who approves a data classification is generating evidence. Every audit lead who opens an inspection case and routes tasks to framework owners is generating evidence.
The evidence trail is not something you build before an audit. It is something that builds itself, because the platform captures every meaningful compliance action as it happens.
That is what a GRC platform provides: the systematic layer between "we do compliance work" and "we can prove it."
What this means for your organization
If your compliance team spends more time assembling evidence packs than doing actual compliance work, the problem is not effort, it is architecture. The work is happening. The evidence is not being captured.
A GRC platform changes that equation. It does not add work. It makes the work you already do produce the evidence you need, automatically, structurally, and in a format that withstands regulatory scrutiny.
If you want to see how this works in practice, how forms, tasks, data mappings, assessments, and approvals become audit-ready evidence as a byproduct of daily compliance operations, explore AesirX ComplianceOne at https://aesirx.io/compliance-one
Ronni K. Gothard Christiansen
Technical Privacy Engineer & CEO @ AesirX.io